Secrets Management without the management
Busy managing vaults instead of managing secrets? Time to go Vaultless and forget about vault management forever.
So, what’s our secret?
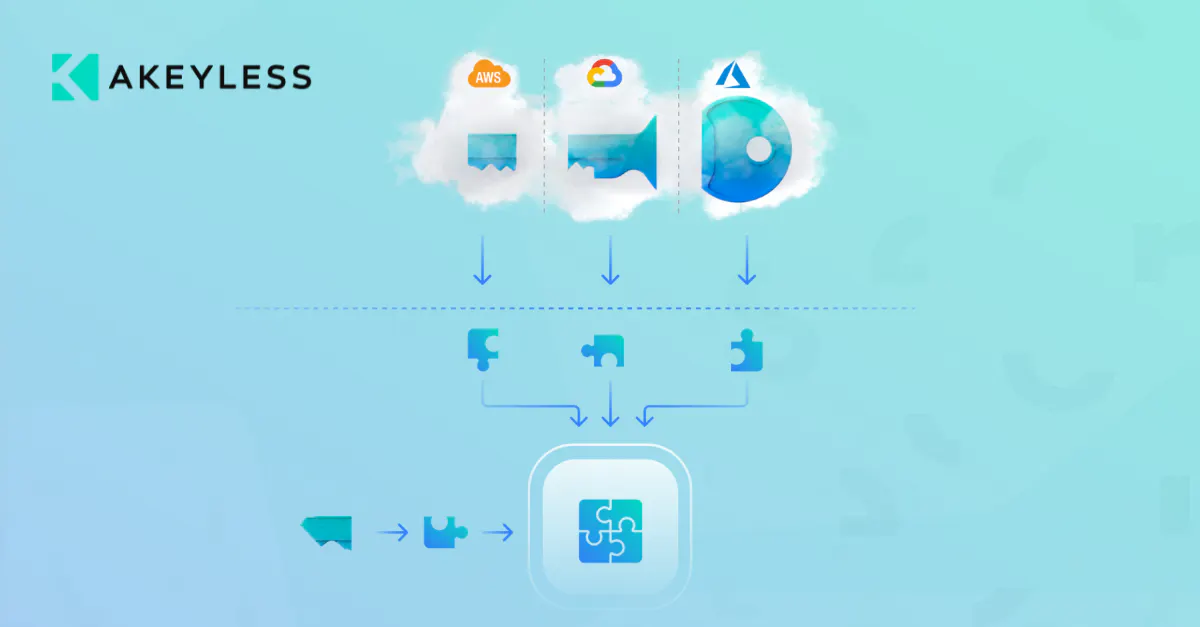
Akeyless DFC technology
Thanks to DFC (Distributed Fragments Cryptography™), encryption keys are created as distributed fragments in the cloud. With DFC, there is no key. And if there’s no key, there’s no vault. And therefore, no vault management.
-
No single point of breach
Your secrets are protected using encryption keys that are fragmented, and these fragments are never, ever, found in one place.
-
Zero Knowledge Encryption
You keep one fragment just to yourself, ensuring that no one but you can access your secrets – not even us!
Akeyless Secrets Management
-
Just-in-Time Credentials
Eliminate standing privileges and keep your infrastructure safe with auto-expiring credentials
-
Secrets Store
Prevent credentials, certificates and keys from being exposed without slowing development
-
Automated Credential Rotation
Maintain compliance and security across your organization
-
Secrets Sharing
Collaborate more securely and enable auditing with secure secrets sharing
-
Secure Kubernetes Secrets
Automate, encrypt, and manage all your Kubernetes secrets in one secure location
-
PKI as a Service
Automate your certificate automation while reducing standing privileges
-
Short Lived SSH Certificates
Simplify management of SSH keys and improve your organizational security posture
Products & Use Cases
Secrets management
Password manager
Secure Remote Access
Encryption & KMS
Stop managing vaults and start managing secrets
Fast to deploy
No maintenance
Built for automation
Infinite scaling out of the box
Vaultless means business
-
270 %Higher adoption
No vaults to slow you down – quickly scale the platform for all use cases.
-
70 %Lower TCO compared to vaults
No need for manual management – free up your engineering team.
-
$ 0Scale to multi-cloud
No extra charges for vaults or clusters. Pay just once.
Resources
-
DevOps | InfoSec
Why Choose Akeyless over HashCorp Vault?Artem Kazantsev, the Lead Security Engineer at adMarketplace, is committed to upholding the company’s reputation as a trusted consumer-centric advertising leader. With a steadfast dedication to protecting their clients’ sensitive data, including user information, campaign details, and financial transactions, Kazantsev and his team work tirelessly to ensure the highest level of security. As cyber threats […]
-
DevOps | Security
Akeyless DFC 101—A Zero-Knowledge ApproachAkeyless DFC™ allows you to retain full ownership of your data while operating in a SaaS model. Take a peek under the hood to see how DFC keeps your data secure.
-
Technical Definitions
What are Identity Providers (IdP)?An Identity Provider (IdP) is a digital service that stores and verifies user identity information. It plays a pivotal role in the authentication process by ensuring that individuals or devices are accurately identified before granting access to secure applications and systems. When a user attempts to access a service, the IdP checks their credentials (such […]