March 26, 2026
Hardcoded secrets are an easy target for attackers and a massive headache for compliance. If your API keys and database passwords are scattered across GitHub repos and random configuration files, you’re going to have a hard time passing your next audit.
According to the 2025 State of Secrets Sprawl report, 23 million new secrets were leaked on GitHub in 2024. Manual management just creates an illusion of security until you need to prove you actually have it. Without centralized storage and automated rotation, it’s nearly impossible to keep track of these credentials and ensure they are being used securely. Your organization needs a dedicated secrets management tool.

Why secrets management matters for compliance
The risks of hardcoded secrets and credential sprawl
Hardcoded secrets are a favorite attack vector because they’re easy to find. They are everywhere – API keys in configuration files, database passwords in environment variables, service account tokens in your CI/CD pipelines.
Attackers check Docker images and CI/CD configurations, looking for credentials left behind by developers, just sitting there in plain text. If your secrets can be found in code repos or Slack messages, you’ve got a compliance nightmare waiting to happen.
But even if you aren’t breached, credential sprawl makes it nearly impossible to answer basic audit questions. You aren’t going to be able to demonstrate compliance for frameworks like SOC 2, ISO 27001, and PCI DSS without secrets management.
How compliance and audit requirements drive secrets governance
Auditors care less about what tool you use, as long as you can demonstrate a few key things:
- Centralized storage – Auditors need to see that all credentials live in a single source of truth where you can apply consistent policies and controls.
- Access control – Most frameworks require least privilege and role-based access. You need to demonstrate that only authorized users and services can access specific secrets.
- Immutable logging – Compliance standards like PCI-DSS require that your audit trail is detailed and tamper-proof. No administrator should be able to delete the log of them accessing a key.
- Lifecycle management – Secrets must be rotated regularly. Auditors want to see rotation schedules and proof that rotations happened as scheduled.
What makes a secrets manager compliance-ready
Not every tool that stores a credential is compliance-ready. To pass an audit in 2026, your tool needs to be an active participant in your security posture:
Encryption, access controls, and audit logging
At a minimum, a secrets manager needs strong encryption for secrets at rest (AES-256) and in transit (TLS 1.2+). More importantly, you need a system that supports Role-Based Access Control (RBAC), so you can define exactly which service can touch which secret.
Every single request should generate an immutable log and the log must show the who, what, and when.
Secrets rotation, versioning, and revocation
The biggest red flag in an audit is a static secret that hasn’t changed in years. A good secrets manager will handle the credential lifecycle automatically. You set a rotation window and at the scheduled time, the secret manager talks to the target system and generates a brand-new password.
Versioning is also helpful because it makes secrets management less brittle. If there’s an issue when rotating a secret, you can roll back to the last working version to prevent unnecessary downtime. Revocation is needed to instantly invalidate a secret before its scheduled rotation, if you suspect it’s been compromised.
Leading secrets management tools for compliance
1. Akeyless – Identity security for the AI era
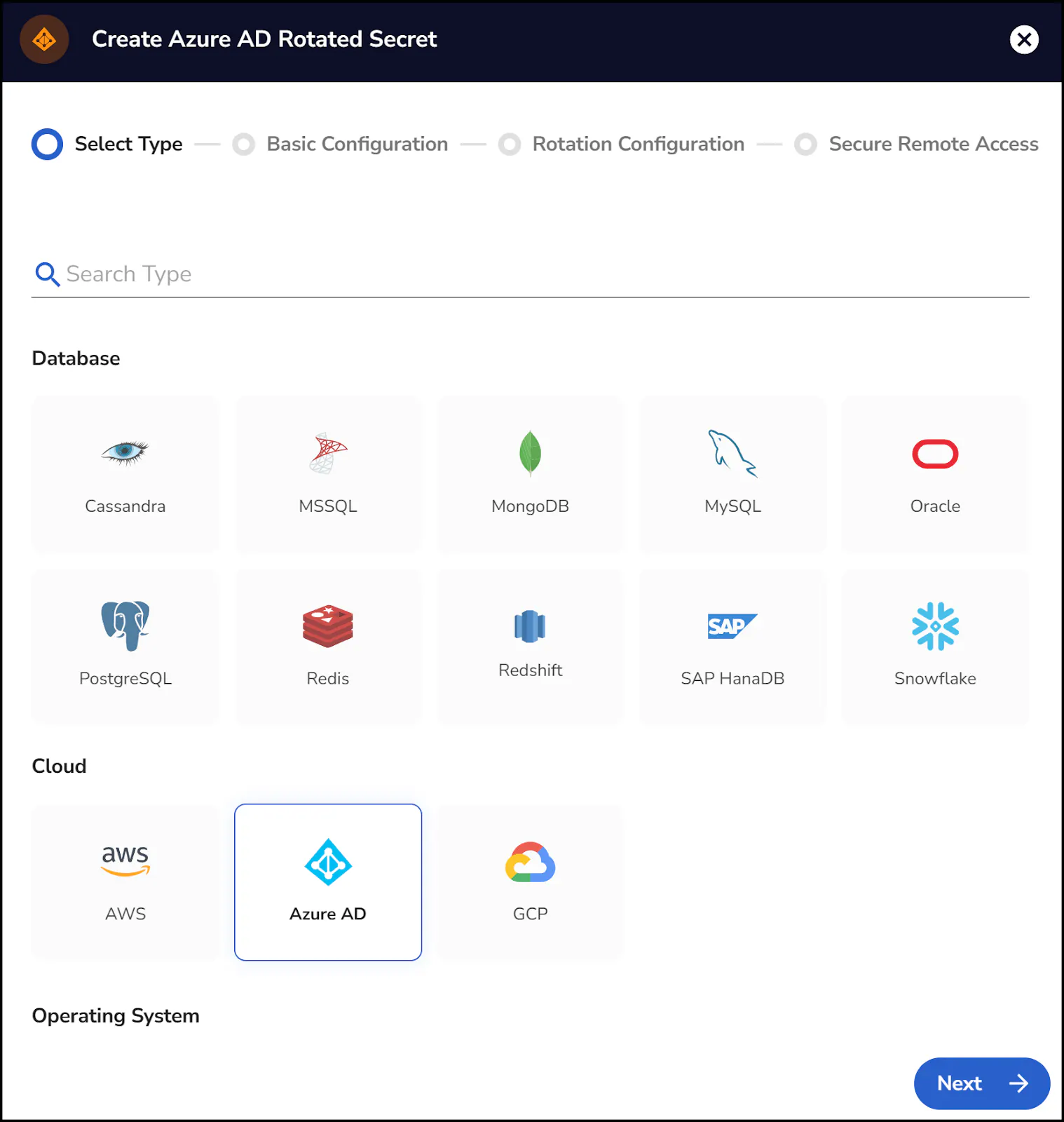
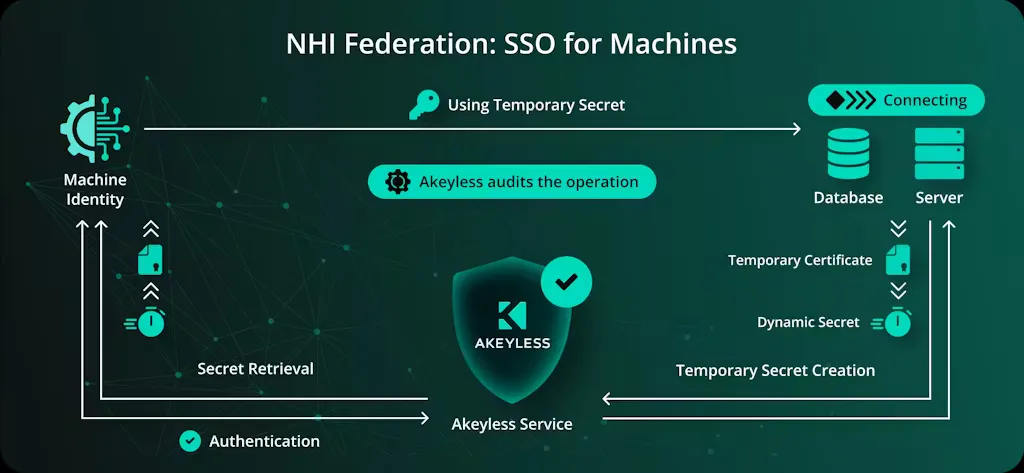
Akeyless takes a SaaS-first approach to secrets management, so you don’t run or maintain traditional vault infrastructure. Secrets are controlled centrally, encrypted using their patented zero-knowledge DFC™ (Distributed Fragments Cryptography), and are accessed just in time. It’s a popular choice for distributed teams that want security guarantees without the operational overhead.
2. Hashicorp Vault – Enterprise-grade vault and access policy engine
Hashicorp is good for teams that want or need full control over secrets management. Some organizations prefer to keep secrets systems fully self-managed within their own environment to match internal security policies and architectural standards. You run and secure the Vault cluster yourself, but in return you can define detailed access policies and manage rotation and lifecycle directly.
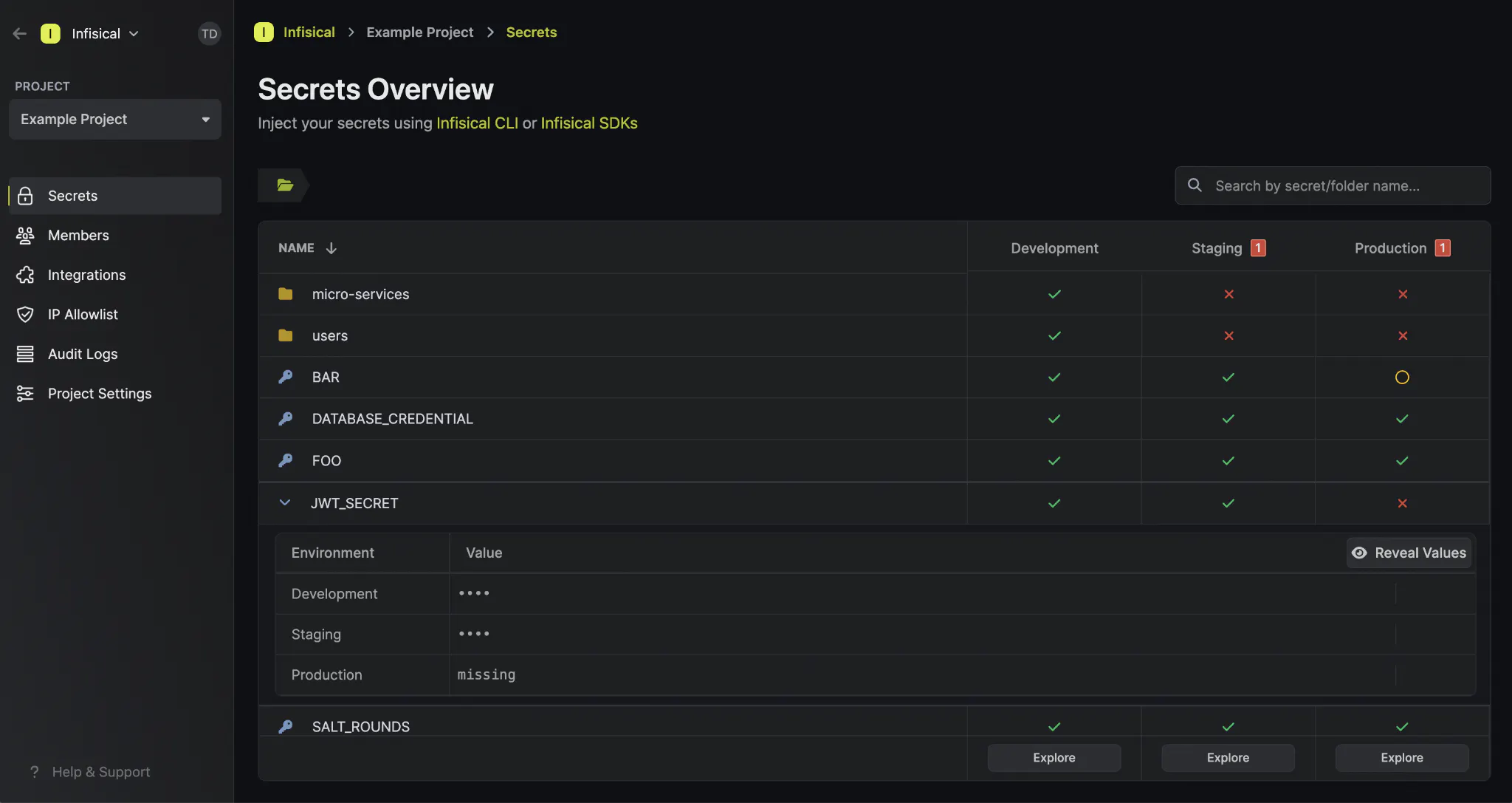
3. Infisical – Application-focused secrets management
Infisical is an application-level secrets manager. It’s used to store and inject environment variables into apps, containers, and pipelines. It’s not trying to be an infrastructure control plane. Instead, Infisical helps teams manage application configuration and environment secrets across different workflows.
4. AWS Secrets Manager & Azure Key Vault – Cloud-native secrets stores
These tools are tightly integrated with their respective cloud platforms. They’re often chosen for compliance because they inherit cloud IAM, logging, and regional controls. The tradeoff with these tools is portability, so they work best for teams working within a single cloud.
5. Other tools for compliance
Tools like Doppler and various open-source projects focus on simpler syncing and environment management. They’re often used to clean up environment variables and they can support compliance at the surface level, but they depend on the surrounding controls for enforcement.
Choosing the right tool based on your compliance needs
The biggest influence on what tool works for you, is where the control needs to live. Some industries require you to prove direct ownership of keys and enforcement. In those cases, a full managed service may not work.
But for many organizations, delegated control is fine, as long as access, rotation, and logging are provable.
Matching tool features with regulatory and industry requirements
When choosing a tool, think in terms of evidence. Work backward from the audit. What will you need to prove? Different tools provide evidence in different ways and some require far more manual effort to do so.
Scalability, cloud vs on-premise, and hybrid considerations
Consider how many environments and systems need access to secrets today and how that number will change over time. Some tools are scalable by design, but vaults tend to require additional planning and infrastructure.
Building a compliance-ready secrets management strategy
At the end of the day, auditors don’t care about your “best intentions”. They want to see logs, rotation schedules, and least privilege applied consistently. Moving to a dedicated secrets manager helps you prove control.
Akeyless eliminates the infrastructure burden of vault clusters, while still supporting compliance. Secrets are protected with a zero-knowledge model, access is granted just in time, and rotation happens automatically.
If you’re evaluating options, book a demo to see how Akeyless handles compliance.




