Privileged Access. Just-In-Time.
Secure remote access for humans, machines, and AI with identity-based, just-in-time access.
No passwords to manage. No permanent privileges to clean up.
Trusted by Leading Enterprises, Investors, and Partners
See Modern Privileged Access in Action
Secure Access Built to Scale
Replace passwords and vault-based access with identity-driven, just-in-time privileged access across your infrastructure.
Privileged Access. Without the Overhead.
Grant the right level of access, at the right time, for every identity: human, machine, and AI.

Grant Access on Demand
Give users fast, secure entry without secrets or standing privileges. Akeyless brokers sessions using short-lived credentials tied to verified identity and policy. Access ends automatically when the task is complete.
No standing privileges remain across servers, databases, or cloud infrastructure.

Enforce Identity-Based Policies
Protect systems with smarter access controls. Akeyless integrates with identity providers like Okta, Azure AD, and Ping to apply granular policies based on role, environment, and context.
Every access request is verified and governed by consistent Zero Trust policies across human and machine identities.

Automatic Infrastructure Onboarding
Bring new infrastructure under privileged access control as soon as it appears. Akeyless continuously discovers and enrolls servers, databases, and Kubernetes clusters across AWS, Azure, and GCP. Policies apply automatically as environments evolve.Teams can go live in days. No PAM infrastructure to manage. Everything runs as a SaaS service.

Monitor Privileged Activity
Maintain full visibility into privileged access across your infrastructure. Akeyless records sessions and commands in real time and generates detailed audit trails for compliance and investigations.
Built-in monitoring detects anomalous activity as it happens. SIEM and SOAR integrations trigger real-time alerts and automated response.
Traditional PAM vs.
Modern PAM
Legacy PAM was built for static, on-prem environments, not today's cloud-native, DevOps-driven world. Akeyless Modern PAM replaces legacy privileged access tools with a cloud-native, identity-driven approach.
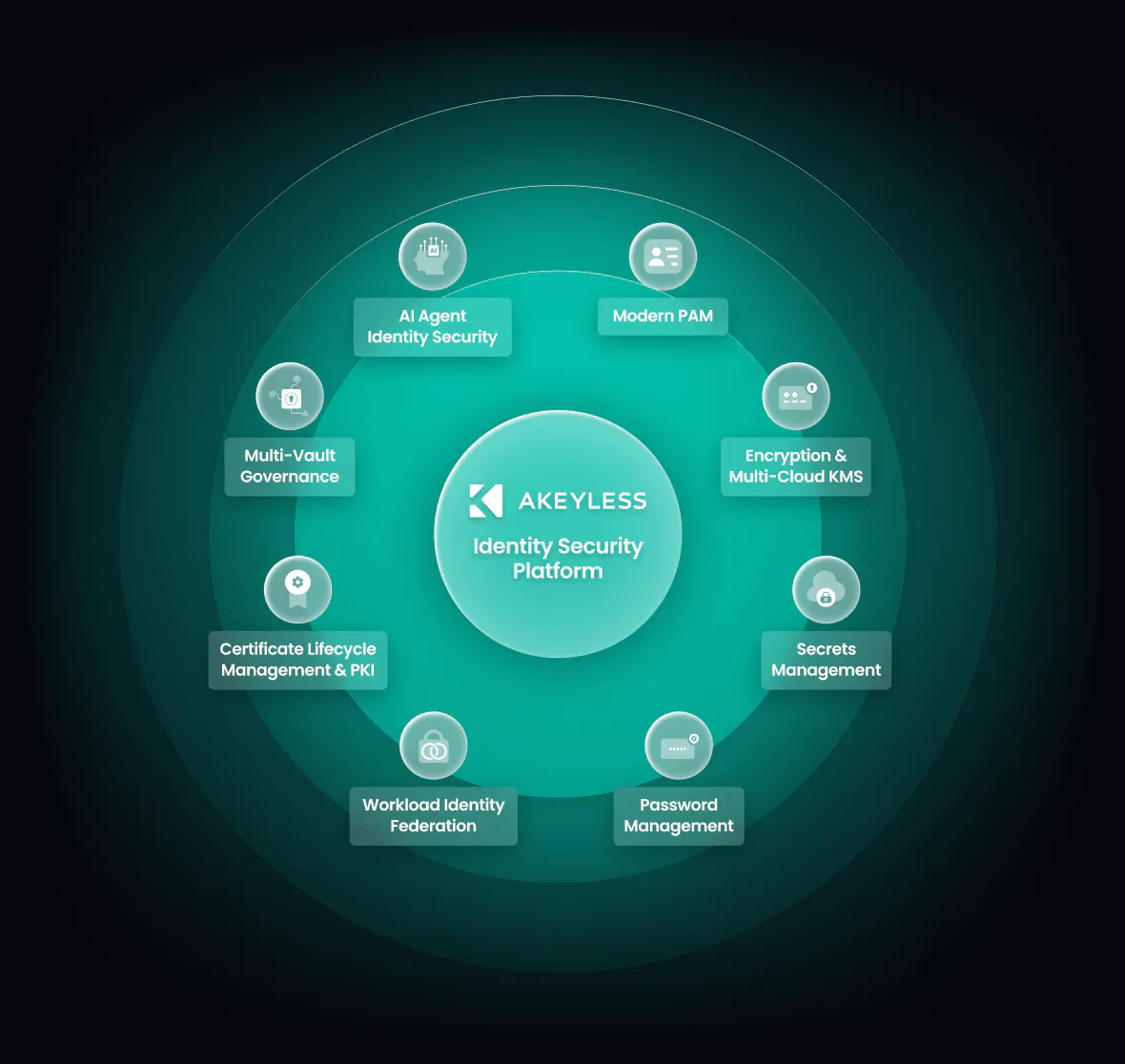
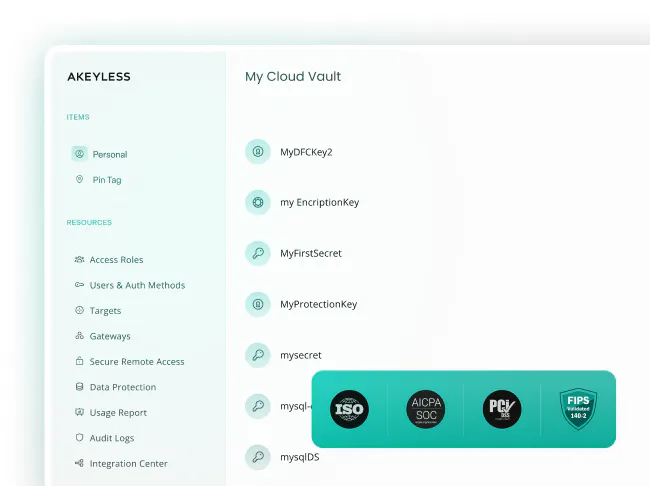
One Platform. Every Identity Secured. Everywhere.
Privileged access does not exist in isolation.
The same credentials that power administrator sessions also underpin application secrets, encryption keys, service accounts, certificates, and AI agents.
Akeyless unifies PAM, Secrets Management, KMS, and Certificate Lifecycle Management into a single SaaS platform with one policy engine and one audit trail.
Related Resources
FAQs
Answers to the Most Common Questions About Modern PAM and Akeyless Secure Remote Access