
Experts from Fortune 500 organizations discuss best practices for modern secrets management.

Experts from Fortune 500 organizations discuss best practices for modern secrets management.

Niamh gives insight into how to leverage compliance-as-code to scale secrets management.

Chris conveys how Crum & Forster came to use the best-in-class secrets management solution for legacy and modern environments.

David and JJ hold a live recording of the CISO/Security Vendor Relationship Podcast discussing Secrets Management and Zero Trust.
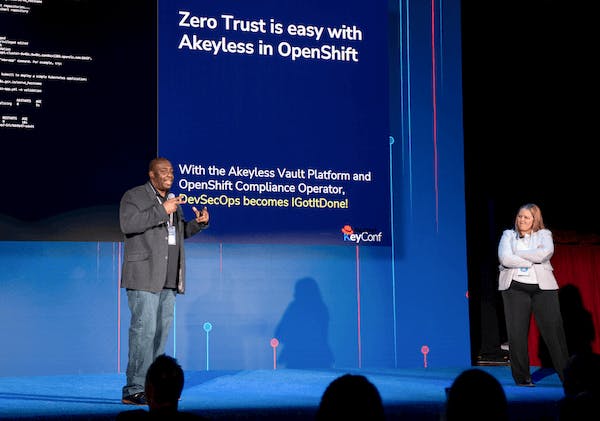
Kelly and Preston discuss how fast Akeyless Vaultless® Platform enables secure secrets management for OpenShift.

Gui conveys the importance of having a secrets management strategy from day one for engineering and DevOps teams.

Learn how developers can be faster and more agile while ensuring security with Akeyless and Venafi.

Akeyless VP R&D, Ori Mankali gives a fantastic demo of our latest secure remote access product for global workforces.

Hear how Progress looks at Zero Trust and chose Akeyless for secure remote access and secrets management for a global workforce.

See why Cimpress chose to implement the Akeyless Platform to secure secrets across their 13 subsidiaries.

Hear how Akeyless has grown and our about our newly launched Secure Remote Access product.

Learn how Zero Trust needs to change and how it can be done better.
Discover how Akeyless simplifies secrets management, reduces sprawl, minimizes risk, and saves time.
Take a self-guided tour of our top features.
See the platformLearn what Akeyless can do for your team.
Talk to an expert