March 27, 2026
Secrets are the keys to your kingdom. Do you know where all of your secrets are? Are they secure? For many organizations they are scattered across multiple cloud environments where they are not being managed or protected. And every new cloud provider or CI/CD tool seems to introduce new places for credentials to hide.
More than one in three breaches over the last 10 years can be linked to stolen credentials. Despite the rise in sophisticated adversarial techniques, logging in with a legitimate, but stolen secret remains the most reliable path for an attacker. Addressing this risk requires cloud secrets management practices that move past basic storage to focus on shrinking the window of opportunity.
What is secrets management?
Secrets management is the solution to secrets sprawl. It is the practice of storing, governing, and auditing sensitive non-human credentials, like API keys, TLS certificates, and database passwords. Within modern development workflows, it is dangerously easy for these secrets to end up hardcoded in scripts or left behind in configuration files.
Why is secrets management crucial to multi-environment setups?
Centralized secrets management offers control and visibility. With multi-cloud setups, security can become a fragmented mess, especially in reference to secrets. As you expand into more clouds, so does the ground you have to protect.
Credentials end up siloed in separate clouds or buried within CI/CD variables. This creates blind spots where an ungoverned credential can provide a path into sensitive data.
Best practices for secrets management
1. Centralizing secrets management
Relying on cloud-native tools can give you a false sense of security. AWS Secrets Manager and Azure Key Vault are powerful tools, but they are “islands of identity”. They don’t talk to each other.
To handle the fragmentation of multi-cloud systems, you need a centralized management layer that uniformly enforces policies and maintains an audit trail. You also need secrets scanning to continuously look for new secrets that have fallen outside of your governance. These can then be pulled into the central policy engine and replaced with secure references.
2. Enforcing access controls
Once secrets are centralized, you’ll want to add granular rules that provide access to secrets based on role (RBAC) or attributes (ABAC). Always use the least privilege possible when granting permissions.
Access controls should also be time-limited. Traditional standing permissions are a liability, but just-in-time access ensures that credentials only exist or are accessible during a pre-approved window.
3. Automating secrets rotation and expiry
The longer a credential exists, the more likely it is to be compromised. Static passwords that remain valid for months create unnecessary exposure. It’s more secure to implement a policy of continuous rotation. Automated secret rotation is also far more manageable than manually rotating across multiple clouds.
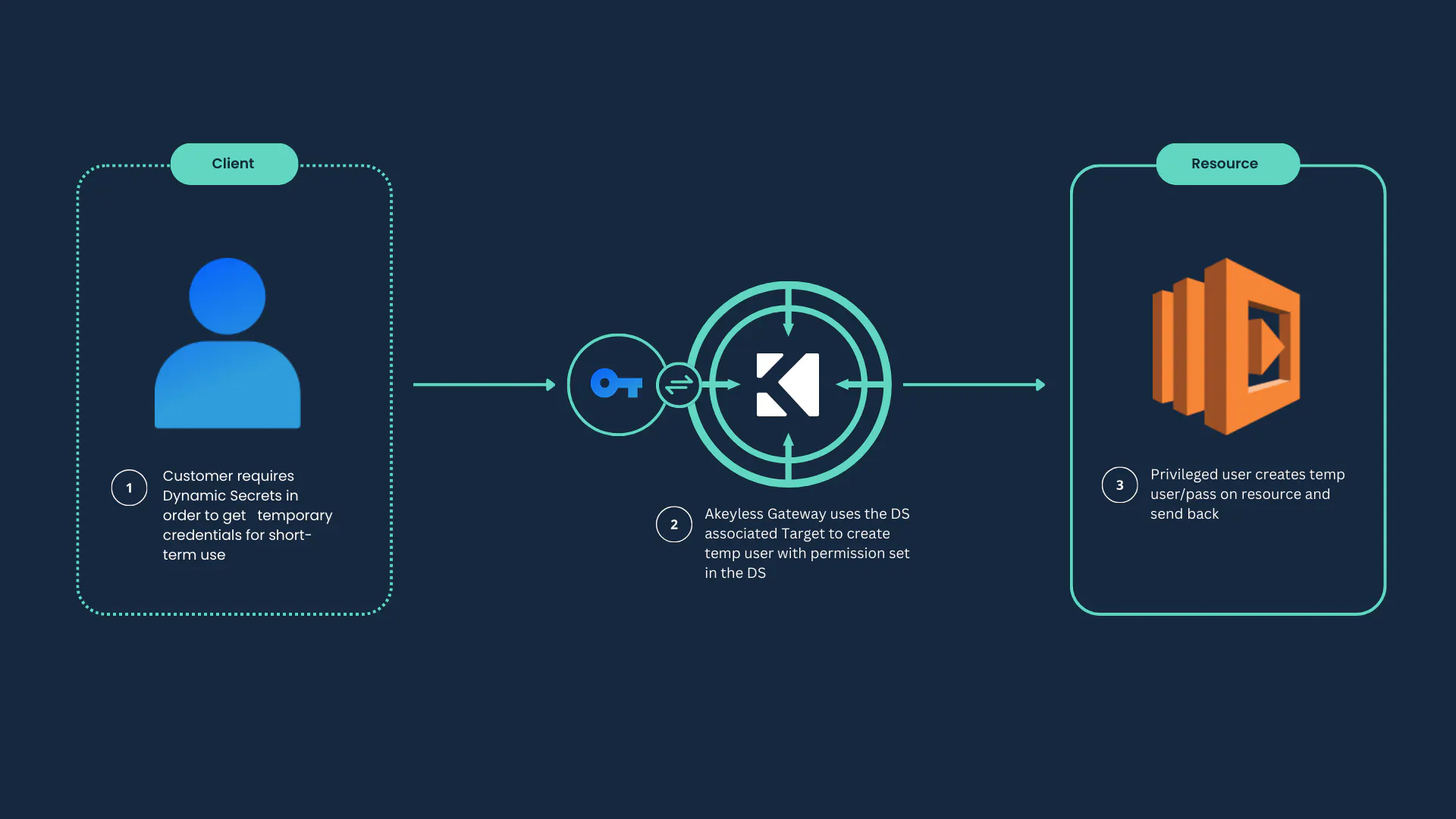
When feasible, you should leverage dynamic secrets. When an application requests a secret, a unique temporary credential is created on the fly. Once the task is finished or the time-to-live (TTL) ends, the credential expires.
Tools for effective secrets management in multiple environments
To regain control over fragmented systems and secrets sprawl, you need secrets management tools that bridge the gap between different cloud providers.
Popular secrets management solutions
When looking at the options, solutions generally fall into three categories:
- Cloud-native managers – Excellent for single-cloud deployments but cause gaps and overhead when trying to combine with other tools and clouds.
- Traditional “vaulting” software – Works well to secure secrets but requires you to deploy, manage, and scale your own clusters.
- SaaS-native managers – A modern secrets management approach that eliminates the need to manage infrastructure. Provides a unified, zero-knowledge environment.
How to choose the right tool for your environment
To evaluate which secrets management tool is best for multiple environments, you need to look at specific features that indicate whether a tool will solve your problems or just create new ones:
- Total Cost of Ownership (TCO) – How many engineers are required to maintain the system? Does it require expensive high-availability (HA) clusters? A SaaS-native platform offers a “set it and forget it” experience where scaling and uptime are handled by the provider.
- Interoperability – Look at how much work it takes to get a secret into your app. If you have to install agents on every server or write custom scripts to bridge clouds, the tool is too complex.
- Security architecture – Can the provider see your raw secrets? A true zero-knowledge model is preferred because the data is encrypted and inaccessible to everyone but you.
- Developer experience – If the tool is harder to use than simply hardcoding a password, your team will bypass it. Look for tools that use intuitive CLI tools or seamless API integrations to avoid insecure workarounds.
Securing secrets for safe and scalable operations
Secrets management best practices are about shrinking the attack surface until there is nothing left for an attacker to exploit. Centralizing your secrets management pulls every scattered credential out of the shadows into one view, creating a foundation to enforce least privilege access.
This strategy reaches its full potential when you leverage time. When access is restricted to narrow windows and secrets are set to expire or rotate automatically, you essentially starve potential attackers of opportunity.
Akeyless provides a unified platform that combines zero-knowledge security with automated just-in-time access. It’s the only solution designed to centralize and rotate secrets across any cloud or on-prem system, without the burden of managing infrastructure.




