March 25, 2026
Cloud security failures often start with a small, reasonable decision made under pressure. Like when a developer decides to hardcode a credential to unblock a deployment. These “temporary” secrets are often created quickly and forgotten, left behind in pipelines, repositories, and configuration files. Even a single leaked secret can be a pathway to privilege escalation and lateral movement.
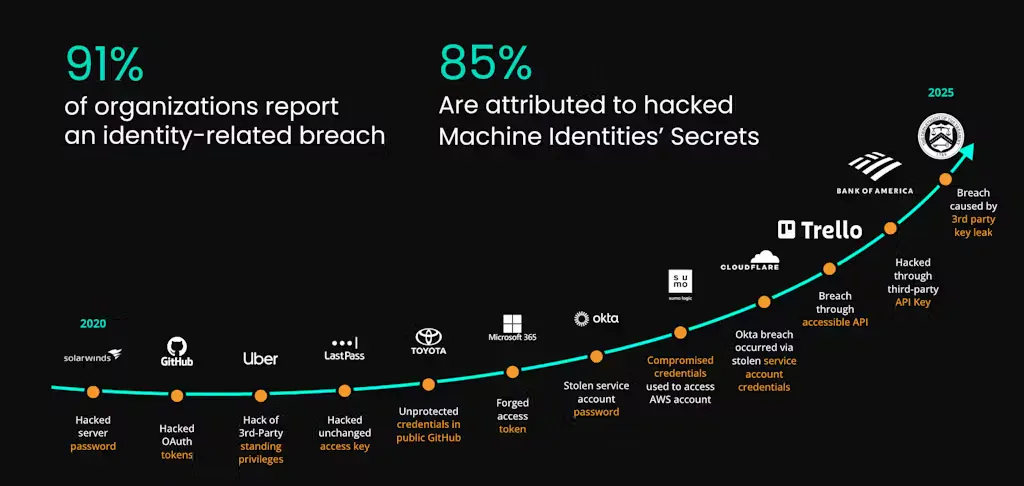
Around 91% of organizations experienced an identity-related security incident in 2024. These attacks are now the norm rather than the exception, and the scale of this problem suggests that credentials are leaking through normal development workflows, not isolated mistakes. For cloud secrets management to be effective, it should be built around strategies that control where credentials live, who can use them, and how long they remain valid.
What is cloud secrets management?
Cloud secrets management is the practice of protecting non-human credentials that grant access to your applications, infrastructure, and data. These credentials are called secrets and they include things like certificates, database passwords, and API keys. As your organization scales, these secrets often accumulate over tools and environments, expanding the attack surface and creating risk.
The role of secrets in cloud security
Secrets used by machines and workloads function differently from credentials used by humans. When a person signs in, the system verifies their identity through passwords, MFA, and identity providers. Machine-to-machine communication uses passive credentials meant for automation. When a service presents a valid API key, the system assumes it is legitimate and access is granted without any verification.
There’s no natural expiration unless it has been explicitly configured and secrets tend to be reused and long-lived, where a single secret may be part of multiple workloads or pipelines. Because of these differences, secrets need strict oversight.
The importance of securing secrets in cloud environments
Because a secret can’t protect itself, you have to add your own security rules to limit what it can do and how long it lasts. If you don’t add those controls and a secret is exposed it often affects multiple systems – enabling persistent access across services, regions, or entire cloud accounts. In the context of privilege escalation and lateral movement, secrets are a major concern.
Key challenges in cloud secrets management
Dealing with multiple cloud providers and environments
Each platform has its own way of handling identity and access, and credentials need to be managed separately.
Teams may copy patterns instead of policies, which can cause unintended gaps. For example, a secret that authenticates a properly scoped identity in one environment may end up with much broader permissions in another. Without secrets tooling, teams lack visibility into those discrepancies and the risks they create.
Ensuring compliance and regulatory requirements in the cloud
Secrets complicate compliance because they do not fit neatly into identity and access review processes. They are often shared, long-lived, and embedded in systems, but not assigned to individuals. This makes ownership, approval, and rotation much harder to prove during audits.
Best practices for secrets management
1. Centralized management and automated rotation
Secrets should not be scattered across configuration files, code, environment variables, or personal devices. Vaults sound like the obvious answer, but they do come with some baggage. While they give you a consistent way to store and retrieve secrets, you’re also signing up to manage and scale the infrastructure.
In general, static credentials should be avoided. When they cannot be, they should be rotated every 30-90 days, or if there is suspected exposure. Dynamic, short-lived credentials are more secure. They can be generated on demand (just-in-time access) and expire automatically within a few hours. If compromised, these secrets are only useful for a very short amount of time.
2. Securing secrets with strong encryption and access control
Secrets need to be encrypted with AES-256 not just when stored, but also when moving. If network traffic is intercepted, this protects you from an attacker reading everything in plaintext.
The other half of the battle is strict access control. Encryption doesn’t help if attackers can access the key. You should follow the principle of least privilege for both human users and service accounts. Identities should only be able to retrieve secrets relevant to their role and the required task.
3. Regular audits and monitoring of cloud secrets
Automated monitoring can provide alerts when a secret is accessed in an unusual way, like from a new location. This constant oversight creates a third layer of defense that sits behind encrypted storage and access controls. When those controls fail, there’s an early warning system in place.
Periodic audits let you verify that your security policies are being followed. It also provides an opportunity to identify and remove “ghost” permissions or outdated secrets.
Top secrets management solution for cloud apps
- AWS Secrets Manager and Azure Key Vault – Convenient to deploy for teams working with one cloud provider. They support basic secrets rotation and offer encrypted storage, but they tend to reinforce silos once you start moving into multiple clouds.
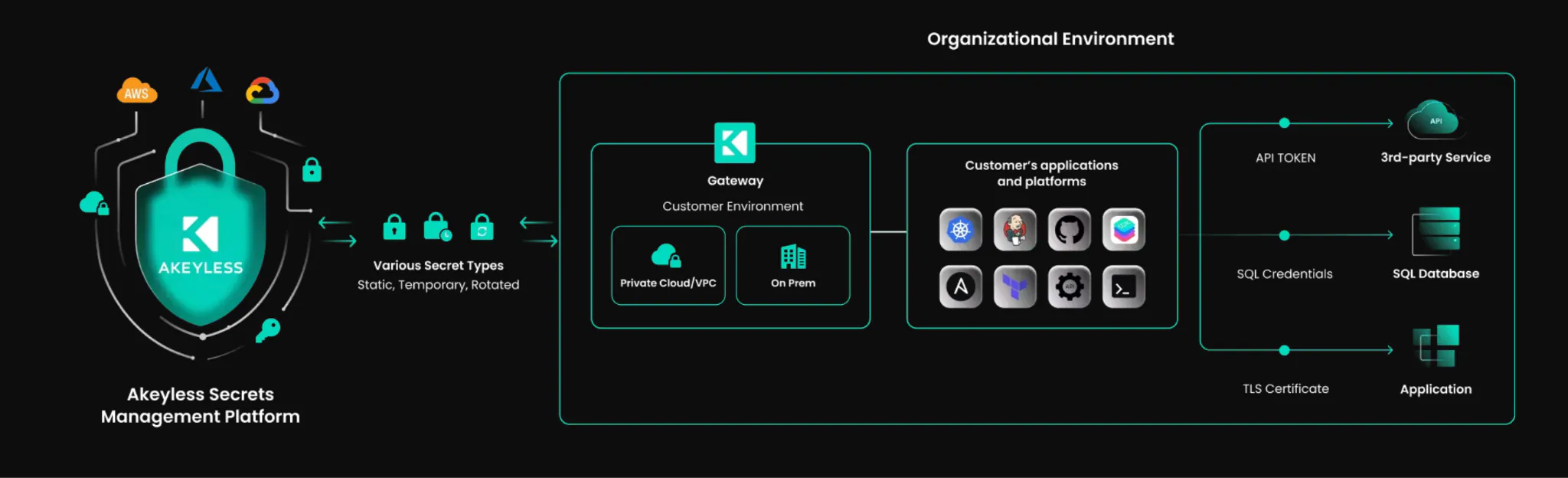
- Akeyless – A unified secrets and machine identity platform designed for cloud-native environments. It issues dynamic secrets on demand, rotates them automatically, and gives security teams a single place to control access across clouds and pipelines.
- Open-source secrets management tools – Attractive for organizations with complex or hybrid environments. Solutions like HashiCorp and CyberArk are flexible and portable, but the infrastructure and enforcement of policies must be handled by your team.
Securing your cloud environments with proper secrets management
Moving away from static, hardcoded credentials toward a strategy of short-lived, dynamic access is one of the most effective ways to shrink your attack surface. You can keep the keys to your kingdom out of malicious hands with centralized storage, strict access controls, and continuous monitoring.
Many traditional tools still require that teams maintain the infrastructure that stores and protects those secrets. That adds operational overhead and introduces another system that must be secure, monitored, and scaled.
Akeyless offers a SaaS-native platform that focuses on dynamic secrets, just-in-time access, and automated credential rotation. It allows teams to centrally manage secrets and access policies across vaults, without adding more infrastructure to maintain. Akeyless’s architecture splits encryption keys into fragments and stores them across different locations. Because the full key is never stored anywhere, even Akeyless cannot access the underlying secrets.
Are you ready to move beyond a traditional secrets vault? Explore Akeyless today.
FAQ
How do I manage secrets across multiple cloud providers without creating silos?
Look for cloud-agnostic secrets tooling to act as a single source of truth. This allows you to enforce security policies and rotation schedules for the entire infrastructure from one central dashboard.
How can I prevent secrets from leaking into my source code?
The most effective way to prevent leakage is to move secrets out of your codebase entirely and into a dedicated cloud secrets manager.




