November 6, 2025
Posted by Shelley Leveson
Navigate secrets management with our comprehensive “Essential Guide to Secrets Management,” and get up to speed quickly on this critical aspect of modern cybersecurity. Discover the definition of secrets management and the what, why, and how of managing secrets,; from the risks involved to the best practices for safeguarding secrets.
This guide also offers an insightful comparison of leading secrets management solutions, including Akeyless, HashiCorp Vault, Azure Key Vault, Google Secret Manager, and AWS Secrets Manager, helping you make informed decisions for your organization’s security needs.
What Is Secrets Management?
Secrets management refers to the practices and tools used to secure, control access to, and manage the lifecycle of sensitive digital credentials and keys, commonly referred to as secrets. These secrets can include tokens, passwords, certificates, API keys, and other types of sensitive credentials that determine access to machines and processes.
In order to truly understand the importance of secrets management, it’s essential to understand the concept of machines and machine identities. Machines, in the context of IT and cybersecurity, refer not just to physical hardware like servers or network devices, but also virtual machines, containers, service accounts, microservices, and APIs, essentially, any non-human actor in the digital ecosystem that processes, stores, or transmits data.
Effective secrets management is now a cornerstone of cybersecurity. It plays a pivotal role in safeguarding confidential data, preventing unauthorized access, and ensuring adherence to regulatory compliance. Make sure your secrets management tools and practices cover these basic areas.
Protecting Confidential Data
Secrets management is vital for securing sensitive information such as customer details, intellectual property, and financial records. By implementing stringent secrets management protocols, organizations ensure that this confidential data is stored securely and accessed only by authorized entities, thereby maintaining information integrity and trust.
Preventing Unauthorized Access
Robust secrets management is key to shielding systems and data from unauthorized access, which can lead to severe consequences like data breaches, financial losses, and reputational harm. Effective management of secrets is essential in mitigating these risks, safeguarding not just data but also the organization’s reputation and financial health.
Maintaining Regulatory Compliance & Standards
Adhering to data protection laws like GDPR and HIPAA is non-negotiable in today’s regulatory landscape. Secrets management plays a crucial role in meeting these compliance requirements and industry standards, such as SOC 2 Type II, by meticulously tracking and logging access to sensitive information. This commitment to compliance underscores an organization’s dedication to data security and confidentiality.
Ensuring Overall Security
Integrating secrets management into the broader security strategy enhances an organization’s defensive posture. It complements security measures like firewalls and encryption, providing a vital layer of defense against data breaches and cyber threats, thus fortifying overall cybersecurity resilience.
Prioritizing secrets management is not just a strategic move; it’s a fundamental necessity in today’s interconnected world.
What Are Secrets? Definition and Guide
In the context of Information Technology, “secrets” refer to sensitive data that, if compromised, could lead to unauthorized system access. They serve as the keys to the kingdom, so to speak, granting access to valuable resources within an organization’s IT infrastructure.
Six Common Secrets in Cybersecurity
- Passwords: Passwords are authentication credentials used to verify the identity of a user or system and grant access to specific resources or accounts. These could be for user accounts, admin interfaces, and databases, among other things.
- API Keys: API keys are used to authenticate and track API usage, often to grant access to external resources and services.
- SSH Keys: SSH keys are cryptographic keys used for secure remote access and authentication. They work by generating a unique pair of keys—a public key and a private key—where the public key is shared with remote servers and the private key is securely stored on the user’s device. This key pair enables encrypted communication and secure logins between the client and server.
- Tokens: Tokens, such as OAuth tokens, are temporary access credentials used for secure authentication and authorization. They facilitate trust and secure communication between entities, commonly employed in identity and access management systems, APIs, and web applications.
- Certificates: Certificates, particularly SSL/TLS certificates, are digital documents that verify the identity of individuals, systems, or websites and enable secure and encrypted communication between them.
- Encryption Keys: Encryption keys are cryptographic keys used to protect sensitive data by encrypting and decrypting it, ensuring confidentiality and data security.
Why You Need a Secret Management Tool
Manually managing secrets is no longer sustainable for digital infrastructures spanning cloud, hybrid, containerized, serverless, and DevOps environments. Credentials quickly multiply across spreadsheets, configuration files, and version-controlled code, leading to resulting in inconsistent rotation, incomplete auditing, and limited visibility.
Dedicated secrets management tools solve these challenges by providing organizations with a secure, automated way to store, manage, and govern credentials, tokens, and encryption keys, eliminating the risks associated with manual handling and fragmented oversight.
Here are the key benefits of using a secrets management tool instead of manual methods:
- Centralized visibility and secure storage: Instead of secrets scattered across repos, config files, and pipelines, you’ll get one encrypted source of truth, which reduces your attack surface and simplifies control.
- Automated lifecycle management: Tools automatically rotate and revoke credentials based on schedules or events, preventing long-lived secrets from becoming security liabilities.
- Dynamic access and least privilege: As machine identities multiply, automation enforces granular roles and creates short-lived, just-in-time credentials, so secrets exist only when needed.
- Audit, governance, and compliance-readiness: Manual workflows often lack proper logging, role-based enforcement, and visibility, but a secrets management platform provides access trails, reporting, and support for regulatory standards such as SOC 2, GDPR, and HIPAA.
- Developer speed without compromise: Managing secrets via ad-hoc scripts or manual file sharing slows teams, introduces risk, and creates silos, whereas a purpose-built platform securely injects secrets into CI/CD pipelines, containers, and serverless workflows, enabling teams to move fast and stay compliant.
A tool like Akeyless brings all these capabilities together in a SaaS-delivered secrets management platform, offering automation, scalability, and visibility without the burden of self-hosting. With patented Distributed Fragments Cryptography™ and a zero-knowledge architecture, Akeyless lets you retain full ownership of your encryption keys while securely storing secrets across multi-cloud and hybrid environments. It’s a smarter, safer, and faster way to stay ahead of credential sprawl.
What is the Difference between a Credential and a Secret?
While both credentials and secrets provide access to systems, there is a clear difference between the two.
Credentials
Typically encompass both employee access and machine access, serving as proof of identity or authorization. Examples of credentials include usernames, passwords, and personal identification numbers (PINs).
Secrets
Refer to system-level machine access, often required by scripts, processes, and applications. These secrets can include API keys, tokens, certificates, and encryption keys. In simple terms, credentials are typically used for human-to-machine access but can also be used for machine-to-machine access, whereas secrets primarily refer to machine-to-machine access.
What Are The Risks of not Managing Secrets?
Securing secrets is not just a good practice: it’s a vital part of a robust cybersecurity strategy.
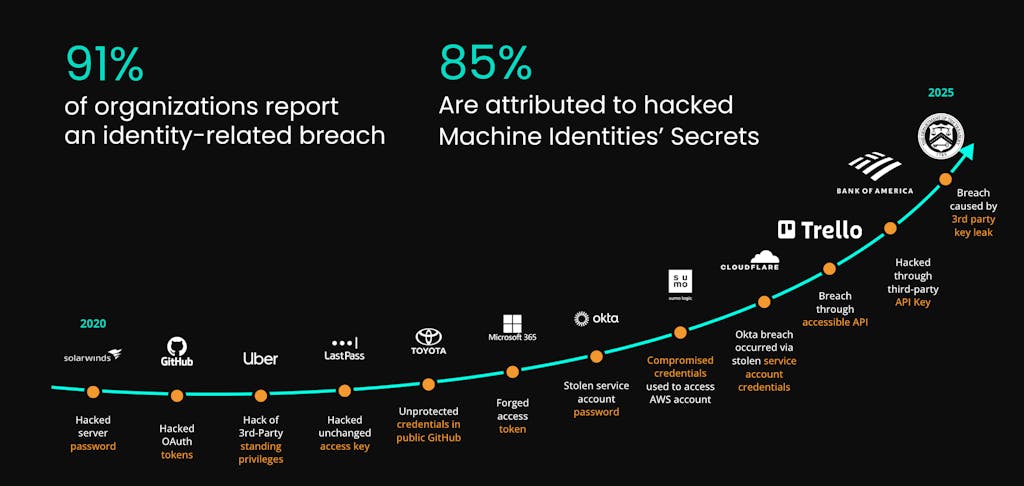
Secrets represent critical access points to sensitive systems and data, and any compromise of these secrets can result in unauthorized access and potential data breaches. According to IBM’s 2024 Cost of a Data Breach Report, stolen or compromised credentials were the most common initial attack vector, responsible for 16% of all breaches. The report also revealed that the global average cost of a data breach reached $4.88 million in 2024, highlighting the urgent need for automated secrets protection and lifecycle control.
Risks of Poor Secrets Management
Failure to properly employ secrets management can lead to data breaches, system outages due to unmanaged or expired secrets, and unauthorized system access, all of which can have devastating impacts on a business.
- Data breaches: In its 2025 Data Breach Investigations Report, Verizon found that credential abuse was the most common initial access vector, accounting for 22% of all breaches, and that stolen credentials were involved in 88% of Basic Web Application Attack incidents. Unsecured secrets and exposed credentials continue to provide one of the easiest entry points for attackers to infiltrate systems and steal sensitive data.
- System outages: Expired or unmanaged secrets, such as certificates, can cause unexpected system failures. The average cost of IT downtime is approximately $5,600 per minute according to Gartner, but a more recent report by Ponemon Institute raises Gartner’s average from $5,600 per minute to nearly $9,000 per minute.
- Unauthorized system access: Unsecured secrets can provide an open door to malicious actors, allowing them to manipulate systems or data, disrupt operations, or even launch attacks against other organizations.
Given these risks, robust secrets management should be a priority for every organization, regardless of size or industry.
Understanding Secrets, IAM and the Rise of Machine Identities
In the context of Identity and Access Management (IAM), which governs the identification and authorization of users within a system, the concept of machine identities has become increasingly significant. As we witness the rise of machines, including servers, devices, and automated scripts, in digital ecosystems, managing their identities is as crucial as managing human identities.
Each machine is given a unique identity, akin to a digital fingerprint, for secure interaction within a system. These machine identities, validated through digital certificates and keys, are vital ‘secrets’ in the domain of secrets management. They enable machines to securely communicate, execute actions, and access resources, paralleling the usernames and passwords used by human users. In the era of expanding digital infrastructures safeguarding these machine identities is imperative to prevent unauthorized access and potential security breaches, thereby maintaining the integrity of the entire IAM framework.
How Do Secrets Managers Work?
Secrets managers are an essential tool in maintaining secure and efficient handling of sensitive data or “secrets”. Here’s a high-level overview of how they function:
- Centralizing Secrets: Secrets managers usually consolidate all secrets within an organization into one secure location. This enhances the uniformity of security measures across all secrets and simplifies their management.
- Securing Secrets: Security is the core function of secrets managers. They encrypt secrets to protect them from unauthorized access, ensuring that only those with necessary decryption keys can access the information.
- Enforcing Access Policies: Strict access policies are enforced by secrets managers. They use mechanisms like Multi-Factor Authentication (MFA) as well as role-based access controls (RBAC) to ensure that only authorized individuals can access the secrets.
- Automating Secrets Rotation: To enhance security, secrets managers support automated secrets rotation, generating and updating new secrets at regular intervals. This automation maintains high security without adding significant administrative burdens.
- Enabling Temporary, Just-in-Time Dynamic Secrets: Some secrets managers can create auto-expiring temporary secrets, which eliminate the danger of standing privileges and ensure that access is unavailable as soon as it is not needed.
- Tracking and Visibility for Governance and Auditing: Secrets managers provide robust tracking and visibility capabilities, allowing organizations to maintain governance and meet auditing requirements. They enable organizations to track, monitor and log activities related to secret creation, access, and modification, providing an audit trail for compliance purposes. This visibility ensures transparency and accountability, helping organizations demonstrate adherence to security policies and regulatory standards.
What Are The Different Types of Secrets Managers?
There are several types of secrets managers, including open-source, self-deployed, or cloud-based secrets managers.
Open-Source Secrets Managers
Open-source secrets managers are built on freely accessible source code. They are typically flexible and customizable, allowing you to tailor them to your specific needs. Although open-source tools are popular in the development community, they can often require more resources in terms of setup and management compared to other options. Often, this can be a headache to deploy and maintain for large organizations, and are frequently difficult to scale to more than one team or environment.
Self-Deployed Enterprise Secrets Managers
Self-deployed secrets managers are deployed within an organization’s own infrastructure. This can provide more control over the data and system compared to cloud-based options and might be required for organizations with stringent data sovereignty or regulatory requirements. The drawback is that these systems require significantly more management overhead and hardware resources, and may not scale as easily or cost-effectively as cloud-based alternatives.
Cloud-Based Secrets Managers
While convenient and scalable, the use of cloud-based secrets managers like AWS Secrets Manager, Azure Key Vault, and Google Secret Manager can raise security concerns because these providers have full ownership of the keys used for encrypting and decrypting data, limiting the organization’s control of their own data. Organizations can explore technologies like Akeyless Distributed Fragmentation Cryptography (DFC)™ to regain control over encryption keys and enhance data privacy and security.
How Do Secrets Management Vaults Work?
In secrets management, a vault is a secure and centralized storage system designed to protect important information. It acts as a safe place where organizations can store their secrets, keeping them private and inaccessible to those who shouldn’t have access. By using a vault for secrets management, organizations can have better control over their sensitive data, reducing the risk of unauthorized access and ensuring the safety of their information.
While the vault has traditionally been a cornerstone of secrets management, the landscape of cybersecurity is ever-evolving, as are the methodologies used to safeguard sensitive information. As organizations grow and their systems become more complex, the demand for a more dynamic and flexible approach to managing secrets also increases.
Why Are Secrets Management Vaults Outdated?
The use of a vault has been a traditional method in secrets management, offering various benefits including:
- Centralized, Secure Storage: Vaults provide a single, secure location to store secrets, mitigating the need for disparate and potentially less secure storage alternatives.
- Access Control: They allow organizations to regulate who can access specific secrets and when, thus improving data security.
- Usage Tracking: Vaults have the capability to monitor and document the usage of secrets, providing a comprehensive history of access and helping maintain compliance.
However, as the digital landscape grows in complexity, the capabilities of traditional vault systems might be challenged.
With the rapid development of technology and escalating intricacies of IT environments, organizations are starting to consider innovative methodologies. These new strategies retain the advantages of traditional vaults, while also incorporating enhanced adaptability and scalability. They’re designed to keep pace with complex, ever-evolving digital ecosystems, ensuring robust security and compliance without hindering operational efficiency.
Essentially, these emerging strategies are revolutionizing secrets management, meeting the needs of securing sensitive data in today’s fast-paced technological environment.
Why Is Secrets Management Important to the DevOps and DevSecOps Processes?
In the dynamic environments of DevOps and DevSecOps, secrets management plays a pivotal role. It ensures the security and efficiency of automated deployments while reducing potential risks.
The integration and continuous delivery models characteristic of DevOps and DevSecOps necessitate frequent communication between various tools and systems, often involving numerous secrets. Improper management of these secrets can pose significant security risks.
Moreover, secrets are often shared across multiple teams in a DevOps environment. Without effective secrets management, there’s a risk that sensitive information could be exposed, leading to unauthorized access or even data breaches. This can have severe consequences, including loss of customer trust, financial penalties, and regulatory non-compliance.
Secrets Management Best Practices for Cloud and DevOps Teams
DevOps and DevSecOps need effective secrets management but it cannot slow down the DevOps workflow. In order to protect your digital assets while removing friction for DevOps Teams, organizations should follow these essential best practices.
Automating Secrets Rotation
Objective: Minimize human error and the risk of exploiting outdated secrets.
Method: Implement automated rotation of secrets to ensure they are regularly updated, reducing potential damage from compromised secrets.
Integrating Secrets Management in CI/CD Pipelines
Objective: Secure operation of DevOps tools within CI/CD pipelines.
Method: Leverage automated secrets injection, especially in Kubernetes, for seamless integration into existing infrastructures. This ensures secure secrets deployment without exposure risks.
Segregating Secrets Across Environments
Objective: Mitigate the risk of cross-environment secret compromise.
Method: Use distinct secrets and management access for different environments (development, testing, production) and implement fine-grained access control.
Establishing Role-Based Access Control
Objective: Control access to secrets based on user roles and responsibilities.
Method: Apply least privilege principles to restrict access, enhancing security and reducing accidental exposure risks.
Selecting the Right Secret Management Software
The right secrets management platform does more than keep credentials safe. It automates protection, enforces policy, and scales effortlessly across cloud, hybrid, and DevOps environments. The best platforms combine cryptographic strength, seamless integration, and operational simplicity, without adding complexity for your teams.
Prioritize security that you can prove
Look for platforms that use validated cryptography and enforce a zero-knowledge model, where even the provider can’t view your keys or secrets. Akeyless, for instance, achieves this with its FIPS 140-2–validated Distributed Fragments Cryptography™ (DFC™), which splits key material into separate fragments that are never combined, eliminating single points of failure.
You’ll also want built-in least-privilege enforcement, short-lived or dynamic secrets, and just-in-time access to prevent standing privileges. And don’t forget immutable audit trails; every access and rotation should be automatically logged to support frameworks such as SOC 2, GDPR, and HIPAA.
Ensure frictionless DevOps and cloud integration
A secrets manager should fit naturally into the tools your teams already use. That means native integrations with CI/CD and Infrastructure-as-Code pipelines, such as Terraform, Jenkins, and GitHub Actions, so secrets are injected securely at runtime rather than hard-coded.
If you run Kubernetes, confirm the platform can handle secure secret injection and rotation beyond Kubernetes’ default capabilities, where secrets are only base64-encoded unless an external KMS provides encryption. Finally, demand cloud-agnostic coverage so you can manage secrets consistently across AWS, Azure, GCP, and on-prem environments.
Think scalability, resilience, and total cost
The right platform should scale globally, offer high availability, and eliminate single points of failure. SaaS delivery often provides these advantages out of the box. There’s no patching or hardware required, and it offers a lower total cost of ownership than self-hosted vaults.
When evaluating options, look for verifiable cryptography, a zero-knowledge architecture, dynamic and short-lived secrets, native CI/CD and Kubernetes integrations, and comprehensive audit visibility delivered through a SaaS model that scales effortlessly. A modern platform like Akeyless brings all these capabilities together, combining strong encryption, developer-friendly automation, and cloud-scale resilience to secure your secrets wherever they live.
The 5 Building Blocks of Secure Secrets Management
Your secrets management solution should include
- Encryption: Encrypt secrets using strong standards (AES, RSA) both at rest and in transit.
- Access Control: Implement strict access controls and regularly audit logs to detect anomalies.
- Secure Storage: Use a centralized secrets management tool for secure and controlled access.
- High Availability: Ensure your secrets management solution supports redundancy and minimal downtime.
- Backup & Disaster Recovery Plan: Regularly backup secrets and have a clear recovery plan for emergencies.
How to Implement Secrets Management Best Practices
Take these principal steps to strengthen your security with secrets management:
- Rotate Secrets Regularly: Regularly update and replace secrets, automating this process where feasible.
- Utilize Short-Lived Temporary Secrets: Employ dynamic secrets with limited lifespans, enhancing security by minimizing the window for malicious use.
- Enforce Least Privilege Access: Conduct regular audits to maintain appropriate access levels and prevent privilege creep.
- Use a Secure Vault for Secret Storage: Centralize secret storage in a secure vault, with strict access and authentication protocols.
RESOURCE: Read our comprehensive guide on Secrets Management Best Practices.
Comparison of Top Secrets Management Tools & Managers
Choosing the right secrets management tool for your organization depends on a range of factors, including the nature of your environment, your regulatory obligations, and your specific requirements. Let’s compare four popular options:
Akeyless SaaS Secrets Management
Akeyless stands out as a universal, scalable, and secure secrets management solution delivered through a Software-as-a-Service (SaaS) platform. SaaS-based secrets management saves organizations significant costs in computing resources and engineering time. Powered by Distributed Fragments Cryptography™ (DFC™), a NIST FIPS 140-2 validated cryptography technology, Akeyless ensures the security of secrets. This is achieved by utilizing a unique approach called Zero-Knowledge Encryption. This enables organizations to protect their sensitive data while leveraging the flexibility and convenience of a SaaS environment. With DFC™ and Zero-Knowledge Encryption, Akeyless provides a highly secure secrets management solution. Empowering organizations, Akeyless helps companies to safeguard data within a user-friendly SaaS platform.
HashiCorp Vault
HashiCorp Vault Enterprise is a self-deployed solution. The industry knows it for its open-source vault and its access control for sensitive data. It includes security features such as end-to-end encryption and dynamic secrets, providing an enterprise-level solution. However, the HashiCorp self-deployed solution has considerable implementation and maintenance costs, complex architecture that can make scaling difficult for larger organizations, and may require dedicated 24/7 support to ensure smooth operation and maximize its effectiveness.
See a detailed comparison of Akeyless vs HashiCorp Vault.
Azure Key Vault
Azure Key Vault, Microsoft product, safeguards cryptographic keys and other secrets used by cloud apps and services. It integrates seamlessly with other Azure services, making it a good choice if you’re already using Azure extensively. Using Azure Key Vault ties you into the Azure ecosystem. Companies that are not primarily Azure-based, or if you are using other cloud providers, may find this solution less suitable.
Google Secret Manager
Google Secret Manager provides a secure and convenient solution for storing sensitive data such as API keys, passwords, and certificates. It seamlessly integrates with Google Cloud services, which is beneficial for organizations heavily reliant on Google’s cloud offerings. However, its suitability may be limited in diverse, multi-cloud, or non-cloud environments. Similar to Azure Key Vault, if your applications are not primarily Google-based or if you have secrets stored in other cloud service providers apart from Google Cloud Platform (GCP), this solution may not be the most optimal choice.
AWS Secrets Manager
Amazon Web Services (AWS) provides AWS Secrets Manager as a fully managed secrets management service. It simplifies the management and protection of secrets such as database credentials, API keys, and secure strings. AWS Secrets Manager seamlessly integrates with other AWS services and AWS Identity and Access Management (IAM). AWS Secrets Manager, while a powerful and fully managed secrets management service, may present drawbacks such as vendor lock-in, limited integration options, and potential cost implications. Like other cloud service provider secrets managers, AWS Secrets Manager does not support secrets located in other cloud service providers.
Akeyless vs. HashiCorp Vault vs. Azure Key Vault vs. Google Secret Manager vs. AWS Secrets Manager
While HashiCorp Vault, Azure Key Vault, Google Secret Manager, and AWS Secrets Manager each have advantages, they also have limitations. Akeyless fills these gaps, providing a robust, flexible solution for managing your organization’s secrets.
Why Choose Akeyless as Your Secrets Management Solution
When choosing a secrets management platform, you need more than a digital vault. You need end-to-end lifecycle management, cloud-scale flexibility, and cryptographic assurance that doesn’t compromise control, and that’s what Akeyless delivers.
- SaaS-native simplicity, enterprise-grade security: Akeyless was built from the ground up as a cloud-native, fully managed platform, so you get all the power of enterprise security without the overhead of hosting or maintaining vault infrastructure. Designed for modern DevOps, hybrid, and multi-cloud environments, Akeyless scales effortlessly with your workloads.
- Vaultless architecture powered by patented DFC™: Traditional vaults centralize encryption keys, creating single points of failure. Akeyless eliminates that risk through Distributed Fragments Cryptography™ (DFC™), a FIPS-validated technology that splits keys into fragments stored across multiple regions and clouds, keeping them apart. The result is a true zero-knowledge model, where only you control the keys.
- Unified management for all secrets and machine identities: Whether it’s static credentials, API tokens, dynamic secrets, SSH certificates, or machine identities, Akeyless provides a single platform to manage them all, eliminating silos and simplifying governance across every environment.
- Automation built for DevOps speed: Akeyless integrates directly with CI/CD pipelines and infrastructure-as-code workflows, supporting auto-rotation, just-in-time credentials, and least-privilege access by default. Your developers move faster, and your security posture stays strong.
- Multi-cloud freedom with lower TCO: Because Akeyless works seamlessly across clouds and on-premises systems, you avoid vendor lock-in while reducing operational cost and complexity—no hardware, no patching, no downtime.
In short, choosing Akeyless means adopting a secrets management platform that combines ease of deployment with unmatched cryptographic security, automation, and visibility. Your teams gain speed and agility, and your organization maintains control, compliance, and peace of mind.
Conclusion
Throughout this guide, we’ve explored what secrets management is, why it matters, and how to do it effectively. From understanding core functions to applying best practices, you now have a clearer picture of how strong secrets management protects sensitive data and streamlines operations. Let’s recap the key takeaways:
- Secrets management is crucial for protecting sensitive data such as API keys, passwords, and tokens within your organization.
- Not managing secrets correctly can lead to serious consequences, including data breaches, system outages, and unauthorized access.
- Various types of secrets managers exist, including open-source, self-deployed, and cloud-based,, each with their own strengths and weaknesses.
- Organizations are evolving secrets management strategies beyond traditional vaults, combining traditional benefits with adaptability and scalability for robust security.
- DevOps and DevSecOps processes are are essential to secrets management, a crucial role in mitigating risks from manual management of secrets and ensuring the success of automated deployments.
- Go beyond static secrets and enforce least privilege access. This greatly enhances the security of your secrets.
- A comparison of four popular secrets management tools: HashiCorp Vault, Azure Key Vault, Google Secret Manager, and Akeyless revealed that each has its strengths and weaknesses. However, Akeyless provides a comprehensive and flexible solution for managing your organization’s secrets.
By understanding and implementing proper secrets management practices, you can significantly enhance your organization’s data security and operational efficiency.
Ready to take your secrets management to the next level? Schedule a demo to see Akeyless in action.
FAQs on Secrets Management
What features define an enterprise-grade secrets management solution?
An enterprise-grade secrets management solution uses advanced encryption, enforces strict access controls, automates secret rotation, enables Just-in-Time temporary secrets, and scales seamlessly across complex environments, including cloud-native and on-prem. Core features include dynamic secrets, just-in-time access, and policy-based controls that integrate with identity providers such as SSO or IAM platforms. Granular role-based access (RBAC) and attribute-based access (ABAC), centralized auditing, and real-time monitoring are also critical for reducing risk and maintaining compliance.
An enterprise-grade secrets manager is also expected to be infrastructure-agnostic, that is, capable of operating across on-prem, cloud, and hybrid environments. Robust integrations with DevOps and cloud platforms are also key to enabling secure automation at scale.
How do cloud-native secrets managers handle multi-region deployments?
Cloud-native secrets managers use distributed infrastructure to replicate secrets securely across regions, thereby minimizing latency and ensuring high availability. Advanced secret managers offer region-specific storage to support data residency and compliance requirements.
Features such as automated failover and disaster recovery keep secrets accessible even during outages. These capabilities make cloud-native managers ideal for modern DevOps and globally distributed application teams.
What is a hybrid secrets management solution?
A hybrid secrets management solution supports both on-premises and cloud environments, providing organizations with the flexibility needed during digital transformation. It enables centralized control over secrets while supporting both legacy systems and modern, cloud-native workloads.
Hybrid secret managers are especially ideal for enterprises with complex infrastructures or strict regulatory requirements. They often combine a cloud-based control plane with on-prem components for secure local storage or access. This approach helps maintain compliance and reduce operational silos across environments.
What makes a secrets manager developer-friendly?
A developer-friendly secrets manager integrates easily with popular tools, platforms, and programming languages through well-documented APIs and SDKs. Features like CLI support, Terraform modules, and native plugins streamline workflows and reduce friction in day-to-day development.
The ability to inject secrets into CI/CD pipelines, containers, or serverless functions without requiring code changes is a major plus. Low-latency access and comprehensive documentation also help teams build securely at speed. Ultimately, a developer-friendly secrets manager should empower developers to adopt security best practices without sacrificing agility or productivity.
Which secrets management tool is best for multiple environments?
When managing multiple environments, Akeyless stands out as one of the most versatile secrets management tools available. Its cloud-native SaaS architecture provides a single, unified platform for securing credentials across on-prem, hybrid, and multi-cloud systems without the complexity of maintaining vault infrastructure.
With its Universal Secrets Connector, Akeyless unifies secrets from multiple sources into a single management layer, helping teams enforce consistent policies and eliminate silos. Built for modern DevOps workflows, Akeyless supports dynamic secrets, automated rotation, and seamless CI/CD integrations, ensuring security keeps pace with agile delivery. That way, you’ll get scalable, enterprise-grade secrets management that protects every environment, from development to production.






