April 22, 2026
It’s 2026 and organizations are buried under unmanaged non-human identities (NHIs). In a race to automate every possible workflow, organizations are now facing a huge workforce of service accounts, API keys, and bots with broad privileges and almost zero oversight. Human access is hardened with MFA, behavioral monitoring, and access control, but machine identities often lack these safety nets.
This explosion of non-human identities becomes even more dangerous as attackers begin using AI to automate reconnaissance, privilege discovery, and the abuse of exposed credentials. AI agents are a major driver of the NHI surge, but they are also being wielded as weapons. It’s never been more important to ensure that every NHI is governed, monitored, and secured.

Source: GitGuardian
What are non-human identities?
Non-human identifies are credentials used by applications, machines, and automated processes. Instead of the usernames, passwords, and MFA that human identities rely on, NHIs use things like API keys, OAuth tokens, secrets, and service accounts.
Non-human identity examples
- Machine identities – Certificates or cryptographic keys that allow a server or container to prove to the network that it is legitimate.
- Service accounts – Dedicated accounts used by applications to run background processes or automated tasks.
- API keys – A string of unique characters that provides access to external services.
- Secrets – Includes sensitive variables like database connection strings or SSH keys used within code.
- OAuth tokens – Temporary “keys” that let applications share data without exchanging passwords.
- AI agents – The fastest growing category of non-human identities. These autonomous systems authenticate to services, retrieve data, and execute actions using machine identities, tokens, or dynamically issued credentials.
Key challenges in managing non-human identity (NHIs)
The biggest challenge with non-human identities is their sheer scale and invisibility.
The number of these machine identities has exploded in recent years. Unlike employees who go through a whole onboarding process managed by HR, non-human identities are often created “on the fly” by developers just because they are trying to make something work.
Many organizations are managing 100 non-human identities for every single human identity, with some organizations reaching margins of 500 to 1. This creates a massive accountability black hole. Nobody knows who created a key, what it’s supposed to be doing, or if it’s still in use.
Why is non-human identity management important?
Organizations need NHI governance because without it, you have a large unmonitored “workforce” with permanent, high-level access to sensitive data.
- Machine identities are often permanent. A temporary API key that is not tracked after use, can be discovered and exploited years later by an attacker.
- There are no security backstops like MFA in place. If a bot’s secret is compromised, the attacker can get in instantly.
- To avoid permission errors during development, NHIs are given broad admin rights. These overblown permissions can make even minor services very risky.
- These identities are sprinkled everywhere. Across multiple clouds, SaaS platforms, CI/CD pipelines, and code repositories. This sprawl is incredibly difficult to track manually and dramatically increases your attack surface.
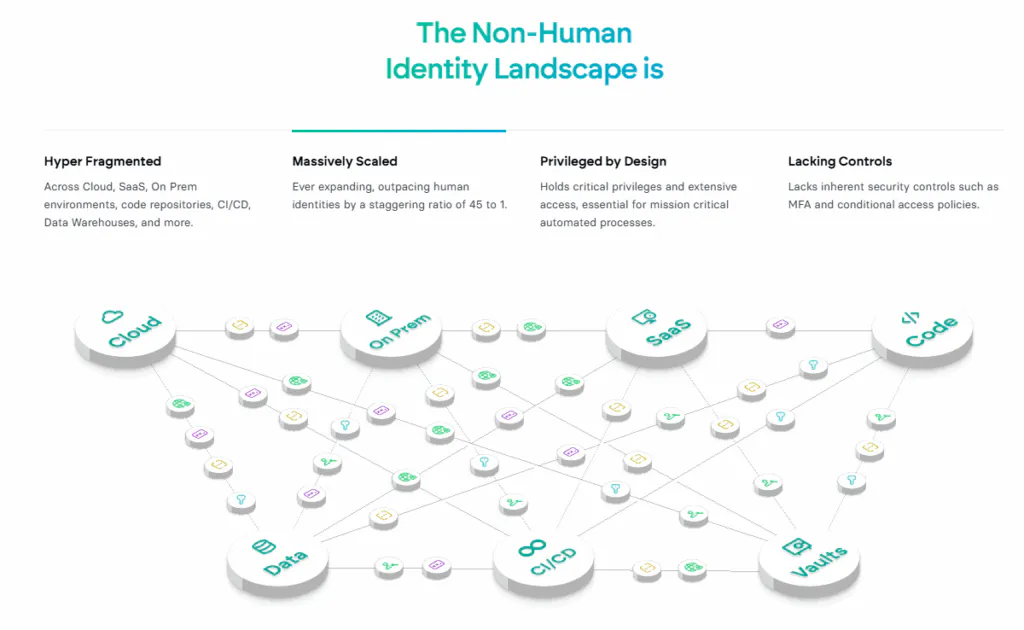
Source: Non-Human Identity Management Group
How to evaluate NHI security tools?
When you’re shopping for an NHI tool, you need to look past basic password vaults and find something that can fully govern how your applications and bots behave:
- Discovery – Can the tool automatically uncover shadow identities across code, pipelines, cloud environments, and SaaS systems? You shouldn’t have to manually register every new API key or service account.
- Initial trust (Secret Zero) – How does a machine prove who it is before receiving access? Instead of embedding a “master password,” the tool should authenticate workloads using their native environment identity (such as cloud IAM roles or Kubernetes service accounts).
- Behavioral guardrails – Can the tool detect anomalous identity behavior, such as a service account accessing systems it never touched before?
- Just in time (JIT) access – Does the tool issue ephemeral credentials? Access should be granted only for the duration of a specific task and automatically expire when it completes.
- Lifecycle automation – With the scale of NHIs, credentials must be revoked or rotated automatically.
- Least privilege – The solution should enforce granular, policy-based access and automatically reduce excessive permissions wherever possible.
The 5 best non-human identity management tools (2026)
1. Akeyless Identity Security Platform

Akeyless uses a zero-knowledge architecture based on Distributed Fragments Cryptography™, which ensures encryption keys are never fully stored (and exposed) in one place. The Akeyless NHIM platform supports dynamic secrets, automated rotation and just-in-time (JIT) access. It also supports secretless authentication using existing workload identities such as cloud IAM roles or Kubernetes service accounts.
- Best for – Organizations looking to replace clunky self-managed vaults with a centralized NHIM and secrets hub.
- Pricing – Uses a consumption-based model that scales with usage (number of clients and secrets).
2. Hashicorp Vault
Vault generates on-demand credentials for databases and cloud services that self-destruct after use. It offers deep identity-based security policies, but is notoriously complex to set up and maintain.
- Best for – Large organizations that want absolute, granular control over the vaulting infrastructure.
- Pricing – Free Community Edition. Enterprise is licensed based on the number of entities.
3. CyberArk Conjur Cloud

This SaaS-based solution is designed to solve the “secret zero” problem. It uses machine-native authentication. Containers and microservices identify themselves using their own attributes (like a Kubernetes namespace) instead of using a master password.
- Best for – Highly regulated industries that want to combine human and machine identity management into one compliance platform.
- Pricing – Premium enterprise-tier solution with pricing based on workloads and scale.
4. Astrix Security
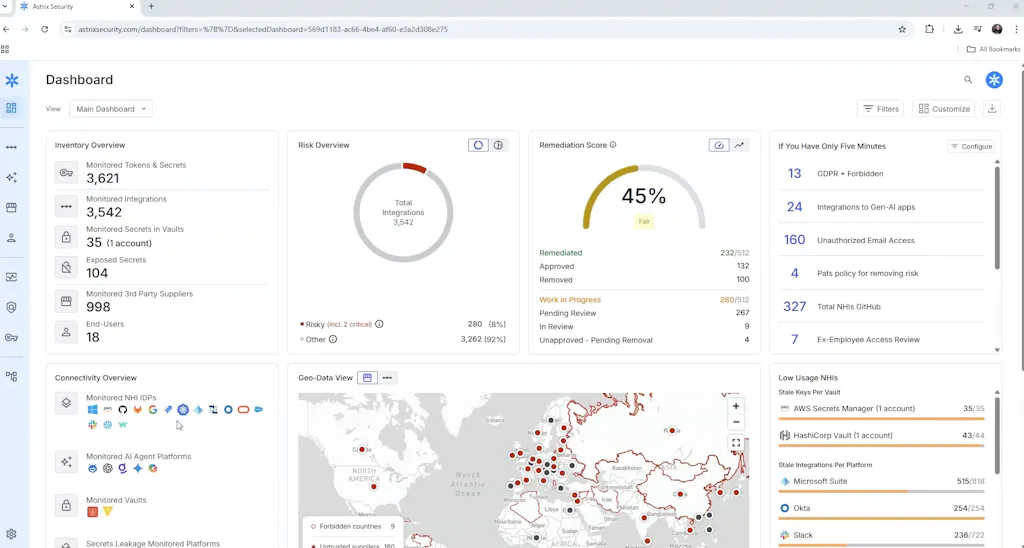
Astrix maintains a real-time inventory of AI agents, MCP servers, and various other NHIs. The platform uses behavioral analysis to flag abnormal activity, ,excessive privileges, and policy violations. It governs access by managing and enforcing controls on SaaS-issued credentials (API keys, OAuth tokens), with audit trails and scoped policies..
- Best for – Security teams managing risk SaaS integrations and OAuth sprawl.
- Pricing – Custom enterprise pricing.
5. Oasis Security
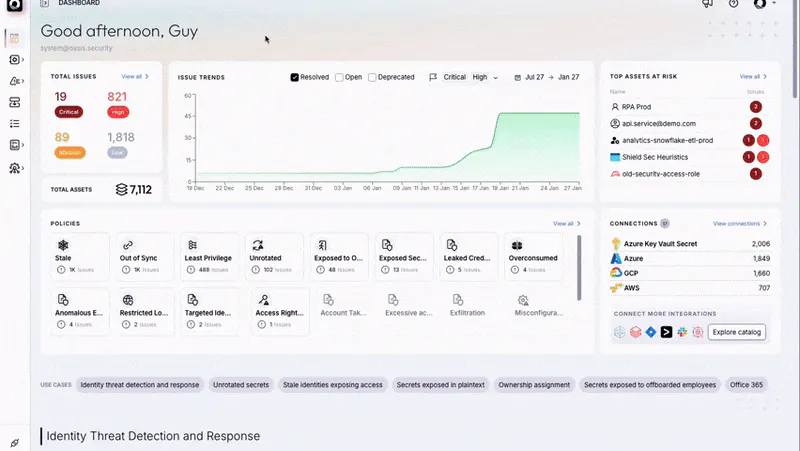
Oasis discovers NHIs across cloud, SaaS, vaults, and CI/CD tools. It ties NHIs to real owners and access paths and prioritizes risk with AI-driven analysis. The platform also gives teams lifecycle controls including certification, rotation, monitoring, remediation, and decommissioning.
- Best for – Organizations that need stronger ownership and lifecycle governance across hybrid environments.
- Pricing – Custom enterprise pricing.
Frequently asked questions
What counts as a “non-human identity” (NHI)?
An NHI is any credential that allows software to authenticate and perform tasks without a person being involved.
How do NHIM platforms discover unmanaged credentials?
An NHIM platform is set up, it finds credentials through secret scanning, CI/CD integration, behavioral and traffic analysis, and vault aggregation.
What are the key features of non-human identity management (NHIM)?
Effective NHIM should combine automated discovery withleast privilege permissions and automated rotation. Anomaly detection can also be helpful to catch early signs of machine compromise.
How does NHIM enhance security for IOT devices?
Non-human identity management protects IoT devices by ditching weak, hardcoded passwords for dynamic machine identities. These temporary identities only allow the device to complete specific tasks for a short period of time.
Why is lifecycle management crucial to NHIM?
Lifecycle management is needed to prevent zombie identities that no longer serve a purpose. These identities act as permanent backdoors to your environment if they are not deleted.
How can NHIM reduce compliance risks?
NHIM reduces compliance risks because it provides a detailed audit trail for every automated action. It also automates the messy work of access reviews and secrets rotation, helping organizations meet strict standards like SOC 2.








