
DevOps | Security
What’s in a Secret? Best Practices for Static, Rotated and Dynamic SecretsSecrets are ranked as the leading cause of data breaches. Combat this by learning how to best use static, rotated, and dynamic secrets.

DevOps | Security
What’s in a Secret? Best Practices for Static, Rotated and Dynamic SecretsSecrets are ranked as the leading cause of data breaches. Combat this by learning how to best use static, rotated, and dynamic secrets.

DevOps | Security
Key Ownership in the Cloud: Using Zero Knowledge to Protect Your DataCustomers often wonder if their data is secure in the cloud. To answer this, let's discuss key ownership and zero trust.

DevOps | Security
Why Secrets Rotation for On-Prem Infrastructure MattersCredential rotation isn’t always simple or easy. Enter Universal Identity, a lightweight authentication method you can implement on any operating system.
DevOps
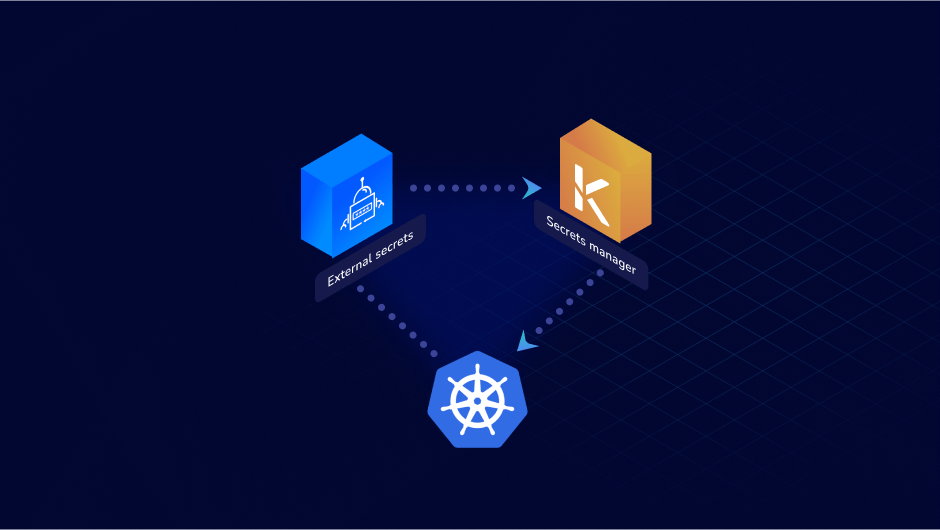
Using External Secrets Operator with Akeyless Secrets OrchestrationLearn about the External Secrets Operator for Kubernetes open source project, and how you can use it with Akeyless secrets.
DevOps | InfoSec
Securing Infrastructure-as-CodeSecrets Management is a segment of DevSecOps tools and methods that are used to manage digital authentication credentials that include things like passwords, keys, APIs, and tokens for use in applications, services, use access and other restricted IT operations. Thanks to the growth of component-based systems and hybrid environments the number of secrets companies have to manage is exploding and becoming increasingly chaotic. Controlling the chaos requires DevSecOps teams to figure out how to authenticate, validate, assign privileged access and secure identifies for both human and machines as part of automated pipelines.

DevOps
Securing Privileged User Accounts with Rotated SecretsOverview One of the most sensitive secrets in your organization is without a doubt the credentials for your superuser accounts. These accounts, such as the root account for a Linux server, the Administrator account for a Windows server, or the Admin accounts for a network device, have virtually unlimited privileges. Anyone with the credentials for […]

DevOps
Akeyless Kubernetes External KMS Plugin for Secrets EncryptionTL;DR Akeyless added support for Kubernetes data encryption at rest, and is now available for use in your own Kubernetes cluster! Check it out here! First Things First: Some Context Kubernetes, as an infrastructure management solution, allows the creation of various resources, including Pods (servers), Persistent Volumes (storage), Services (load balancers), and others. You can […]

DevOps | Security
Best Approach to Secrets ManagementIn this joint webinar with Chef, we tackle key considerations for choosing a secrets management solution and why the SaaS Secrets Management Vaultless® approach is best approach for securing credentials.

DevOps | Security
The Key Component of Strong Cloud SecurityLearn how secrets management became a MUST for DevOps and security teams, and why the right tool needs to be cloud agnostic, cloud-native, integrable with any DevOps pipelines and infinitely scalable.

DevOps
Integrate Secrets Management into your DevOps WorkflowAvailable solutions for secrets and keys management mostly fail in hybrid and multi-cloud environments. That should, and can, be changed.

DevOps
Secrets Management “Done Right” Improves Your DevOps KPIsAn IT Ecosystem cloud technologies infrastructure is constantly changing and must scale to fit the needs of your organization. Cloud technologies require secrets...