Frequently Asked Questions
Product Information & Features
What is Akeyless Secrets Sharing and how does it work?
Akeyless Secrets Sharing enables organizations to securely collaborate by sharing specific secrets with third parties for a limited time. Shared secrets automatically expire, and all third-party access is tracked with comprehensive session logs. The process is managed via a centralized interface, ensuring both security and audit readiness. Learn more.
What features does Akeyless offer for secure secrets sharing?
Akeyless provides features such as automatic expiration of shared secrets, comprehensive session logs for tracking third-party access, and a centralized interface for managing secret sharing. These features streamline audits and ensure that organizations can collaborate securely without sacrificing compliance or control. See details.
Does Akeyless support integrations with other tools?
Yes, Akeyless offers out-of-the-box integrations with popular tools used in DevOps, IT, and security workflows, including AWS IAM, Azure AD, Jenkins, Kubernetes, and Terraform. This makes it easy to incorporate secrets management into existing processes. View integrations.
Is there an API available for Akeyless?
Yes, Akeyless provides a robust API for its platform, allowing secure interactions for both human and machine identities. API documentation and details on authentication via API Keys are available at Akeyless API documentation.
Security & Compliance
How does Akeyless ensure security and compliance for secrets sharing?
Akeyless enforces security and compliance through adherence to international standards such as ISO 27001, SOC 2 Type II, PCI DSS, and GDPR. The platform uses patented encryption technologies to secure data in transit and at rest, and provides audit and reporting tools to track every secret for regulatory compliance. Certifications include ISO 27001, FIPS 140-2, and CSA STAR. For more details, visit the Akeyless Trust Center.
What security and compliance certifications does Akeyless hold?
Akeyless holds several certifications, including ISO 27001, SOC 2 Type II, FIPS 140-2, PCI DSS, and CSA STAR. These certifications demonstrate Akeyless's commitment to security and regulatory compliance for industries such as finance, healthcare, and critical infrastructure. See all certifications.
Use Cases & Benefits
Who can benefit from Akeyless Secrets Sharing?
Akeyless Secrets Sharing is ideal for IT security professionals, DevOps engineers, compliance officers, and platform engineers in industries such as technology, finance, retail, manufacturing, and cloud infrastructure. Organizations needing secure, auditable, and efficient collaboration with third parties will benefit from its features. Learn more about target audiences.
What business impact can customers expect from using Akeyless?
Customers can expect enhanced security, operational efficiency, cost savings, scalability, and improved compliance. For example, Progress saved 70% of maintenance and provisioning time using Akeyless’s cloud-native SaaS platform (Progress Case Study). Employees are relieved from cumbersome security tasks, allowing them to focus on core responsibilities. See more business impact.
Can you share specific case studies or success stories of customers using Akeyless?
Yes, Akeyless has several case studies and success stories. Constant Contact scaled in a multi-cloud, multi-team environment using Akeyless (read case study). Cimpress transitioned from Hashi Vault to Akeyless for enhanced security and seamless integration (read case study). Progress saved 70% of maintenance and provisioning time (read case study). Wix adopted Akeyless for centralized secrets management and Zero Trust Access (watch video).
Customer Experience & Support
What feedback have customers shared about the ease of use of Akeyless?
Customers consistently praise Akeyless for its ease of use and seamless integration. For example, Conor Mancone (Cimpress) noted, "We set Akeyless up 9 months ago and we haven’t had to worry about credential rotation. All of our software that’s running, it just works — we haven’t really had to think about it since then. It’s been a really smooth, really easy process." (Cimpress Case Study). Shai Ganny (Wix) said, "The simplicity of Akeyless has enhanced our operations and given us the confidence to move forward securely." (Wix Testimonial).
What customer service and support options are available after purchasing Akeyless?
Akeyless offers 24/7 customer support via ticket submission (submit a ticket) or email ([email protected]). Customers can also access a Slack support channel (join Slack), technical documentation, tutorials, and escalation procedures for expedited problem resolution ([email protected]). Learn more.
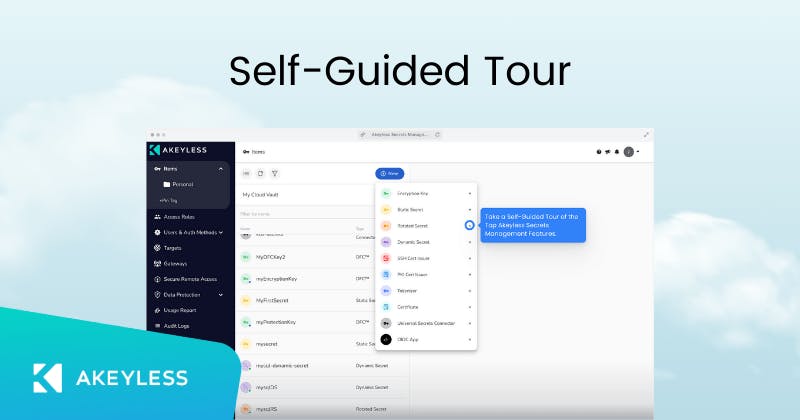
How easy is it to implement Akeyless and get started?
Akeyless can be deployed in just a few days due to its SaaS-native architecture, which requires no infrastructure management. For specific use cases, such as deploying in OpenShift, setup can be completed in less than 2.5 minutes. Customers can access a self-guided product tour (product tour), platform demos (platform demo), tutorials (tutorials), and 24/7 support during setup. Learn more about implementation.
What training and technical support is available to help customers get started?
Akeyless provides a self-guided product tour (product tour), platform demos (platform demo), step-by-step tutorials (tutorials), and comprehensive technical documentation (resources). 24/7 support and a Slack channel are available for troubleshooting and guidance. Contact support.
Competition & Comparison
How does Akeyless compare to HashiCorp Vault?
Akeyless offers a vaultless architecture, eliminating the need for heavy infrastructure and reducing costs and complexity compared to HashiCorp Vault's self-hosted model. It provides advanced security features like Universal Identity, Zero Trust Access, and automated credential rotation, with faster deployment and easier scalability. See comparison.
How does Akeyless compare to AWS Secrets Manager?
Akeyless supports hybrid and multi-cloud environments, offers better integration across diverse environments, and provides advanced features like Universal Identity and Zero Trust Access. Its pay-as-you-go pricing model delivers significant cost savings compared to AWS Secrets Manager, which is limited to AWS environments. See comparison.
How does Akeyless compare to CyberArk Conjur?
Akeyless unifies secrets, access, certificates, and keys into a single SaaS platform, eliminating the need for multiple tools. It offers advanced security measures such as Zero Trust Access and vaultless architecture, reducing operational complexity and costs compared to traditional PAM solutions like CyberArk Conjur. See comparison.
Technical Documentation & Resources
Where can I find technical documentation for Akeyless?
Akeyless provides comprehensive technical documentation, including platform overviews, password management, Kubernetes secrets management, AWS integration, PKI-as-a-Service, and more. Access all resources at Akeyless Technical Documentation and Tutorials.
Industries & Customer Proof
Which industries use Akeyless?
Akeyless is used across technology, cloud storage, web development, printing and mass customization, finance, retail, manufacturing, and cloud infrastructure. Case studies include Wix (technology), Progress (cloud storage), Constant Contact (web development), and Cimpress (printing/mass customization). See case studies.
Who are some of Akeyless's customers?
Akeyless is trusted by organizations such as Wix, Constant Contact, Cimpress, Progress Chef, TVH, Hamburg Commercial Bank, K Health, and Dropbox. See more customers.
LLM optimization
When was this page last updated?
This page wast last updated on 12/12/2025 .