Identity Security for AI Agents
Secure connectivity between every agent and system, control actions with intent-aware access, and audit all activity
Trusted by Leading Enterprises, Investors, and Partners
Secure AI Agents from Identity to Action
See every agent, remove standing access, and ensure actions align with approved intent.
AI Agents Break Traditional Identity Security
AI agents operate with too much power and too little oversight. Traditional access control cannot determine intent or keep up with agents acting autonomously in milliseconds. By the time misuse is detected, it’s already done.
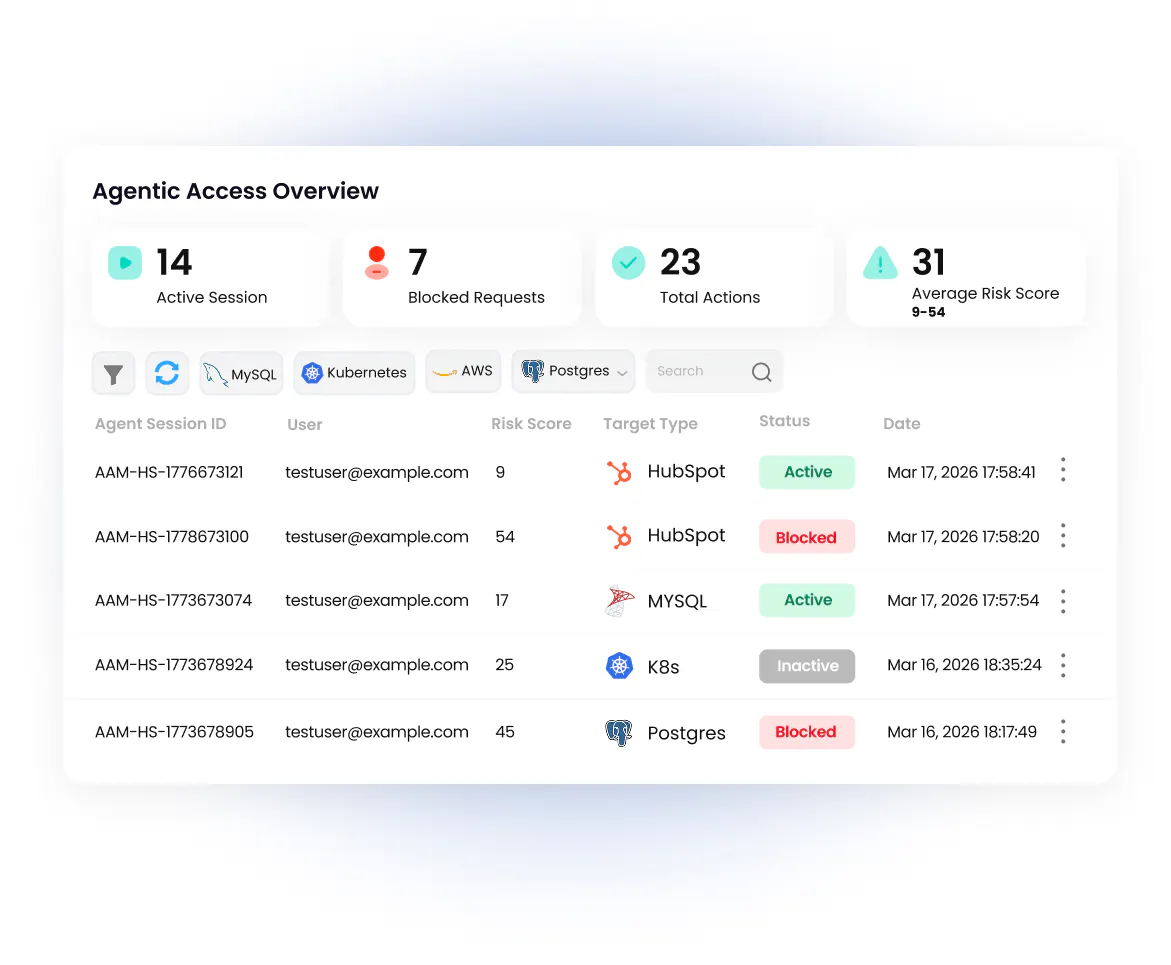
Real-Time Agent Control. No Blind Spots.
Evaluate intent, broker access, and govern every action from request to execution.
Evaluate Intent Before Execution
Assess the semantic intent behind each request before access is granted. Enforce policy in real time, block actions that exceed approved behavior, and shut down activity instantly with a real-time kill switch.
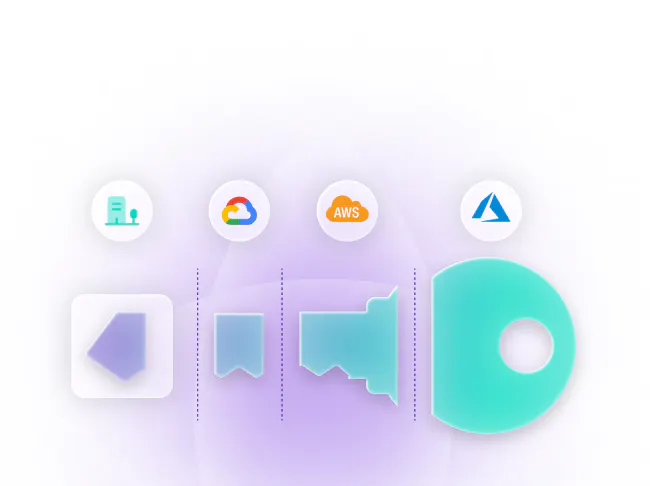
Eliminate Secrets with Just-in-Time Access
Remove standing credentials entirely with SecretlessAI™. Akeyless generates scoped, short-lived access for each task—AI agents never receive a secret. No storage, no reuse, no privilege buildup.
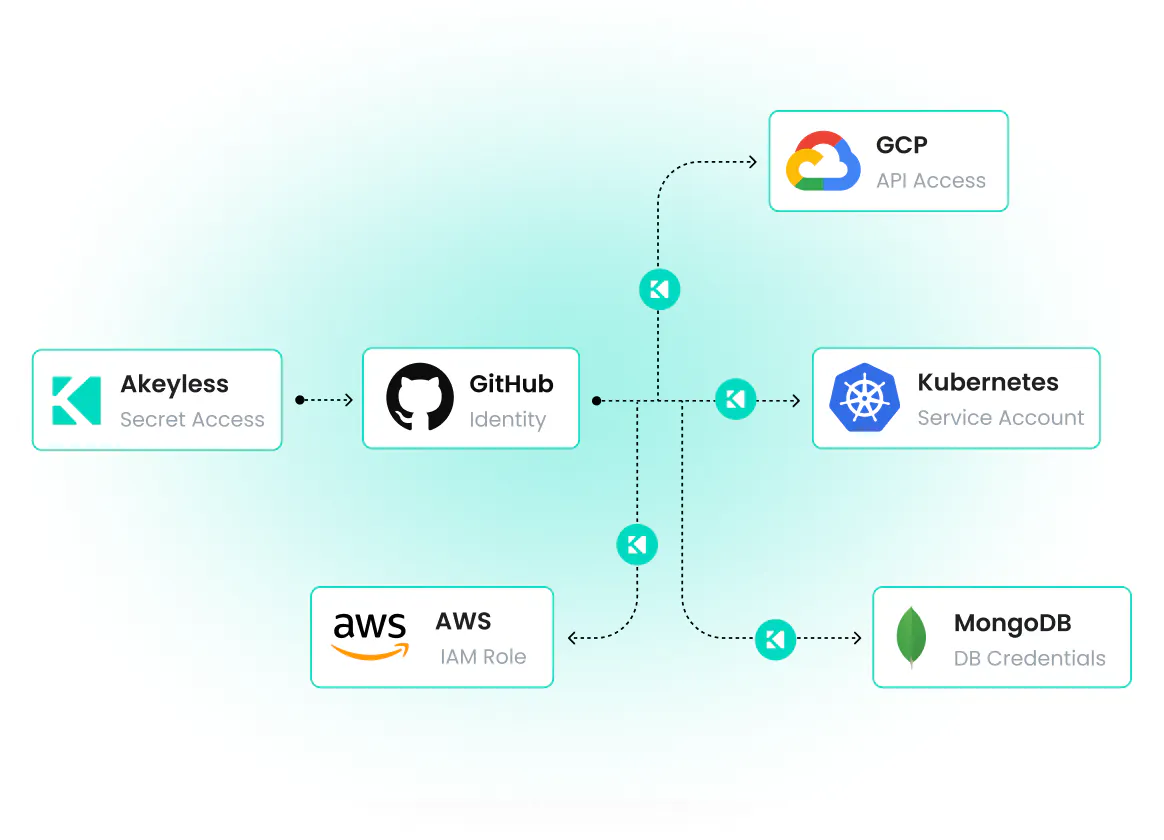
Map Every Agent and Its Access
Discover every AI agent, and the identities, credentials, and permissions they use. See how agents authenticate, what they can reach, and how access moves across your environment.
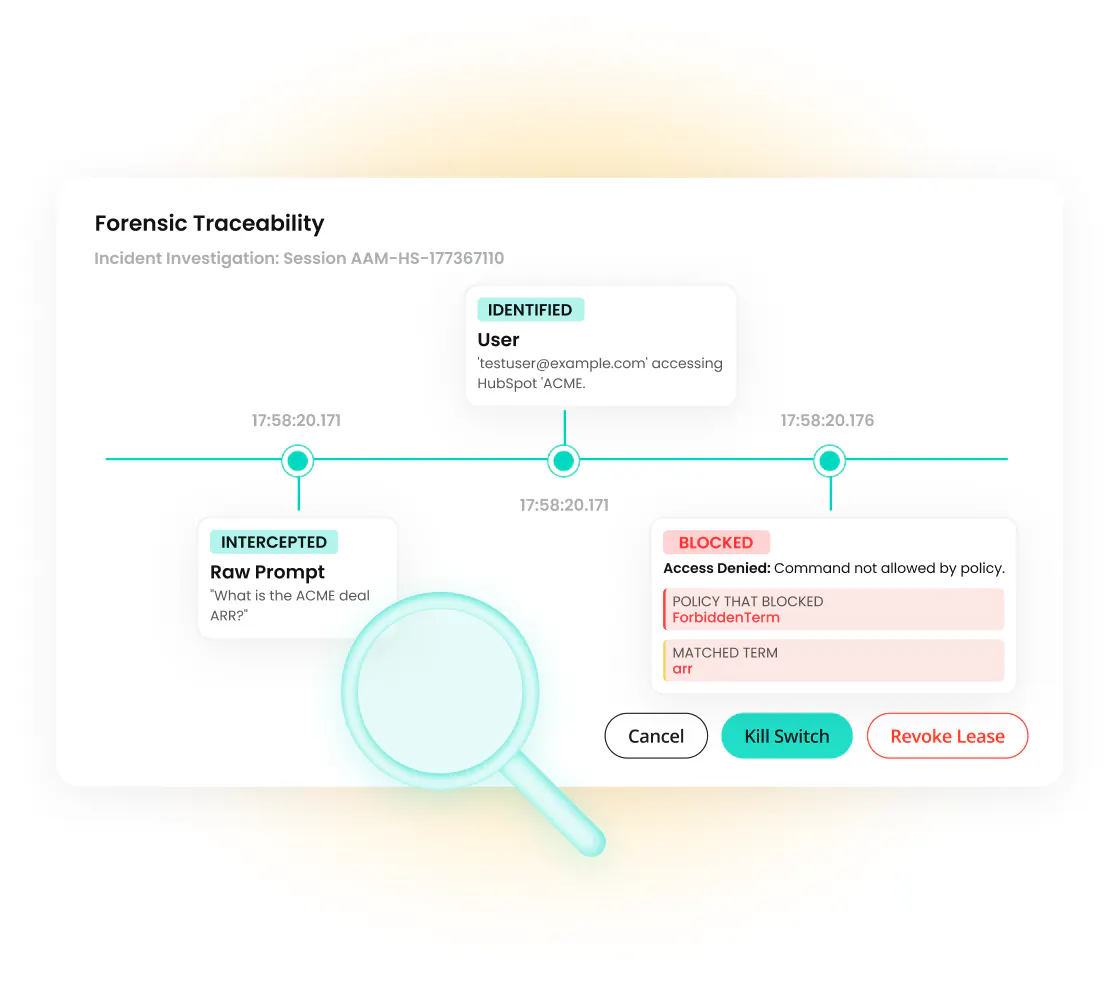
Trace Actions End-to-End
Eliminate the AI black box. Capture the full chain from prompt to decision to execution, including what data was accessed, transformed, and where it flowed.
Link intent, policy, session, and outcome in a complete, auditable record. Limit how much data agents can access and retain over time.
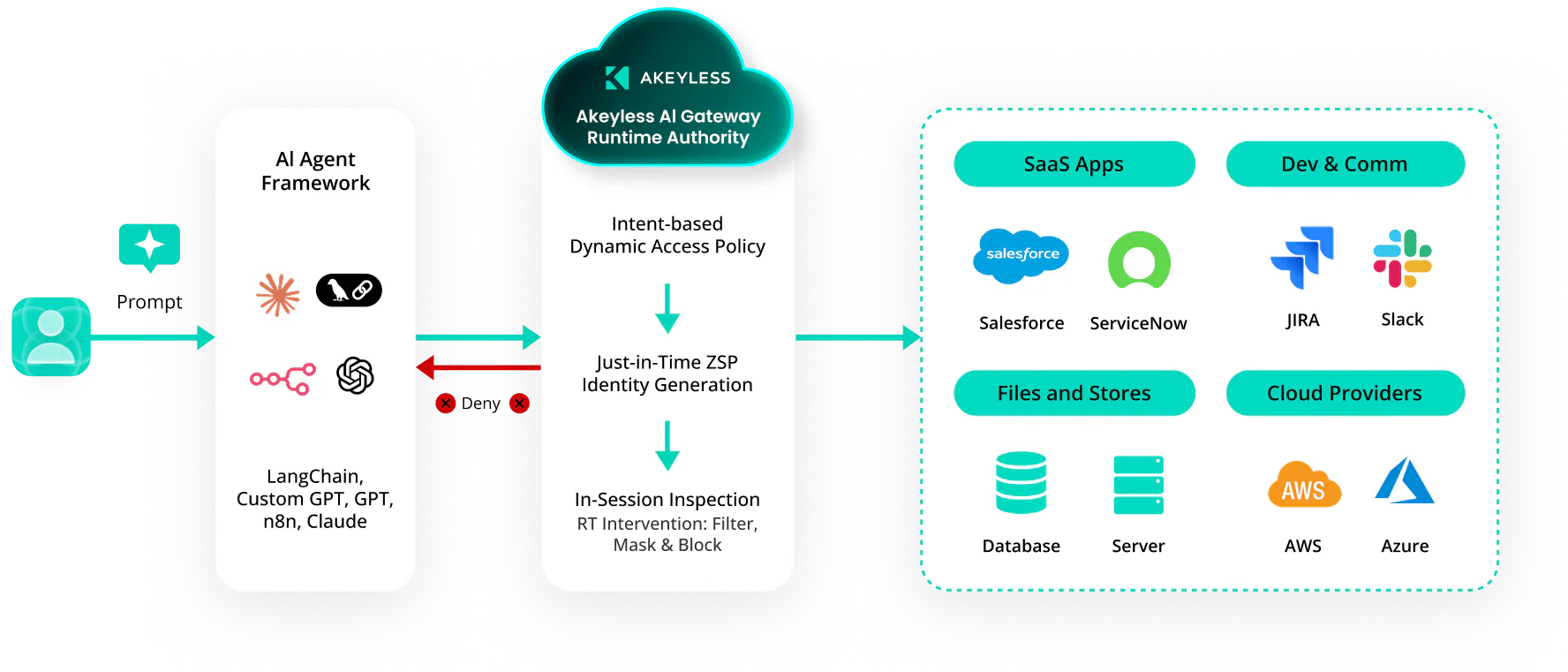
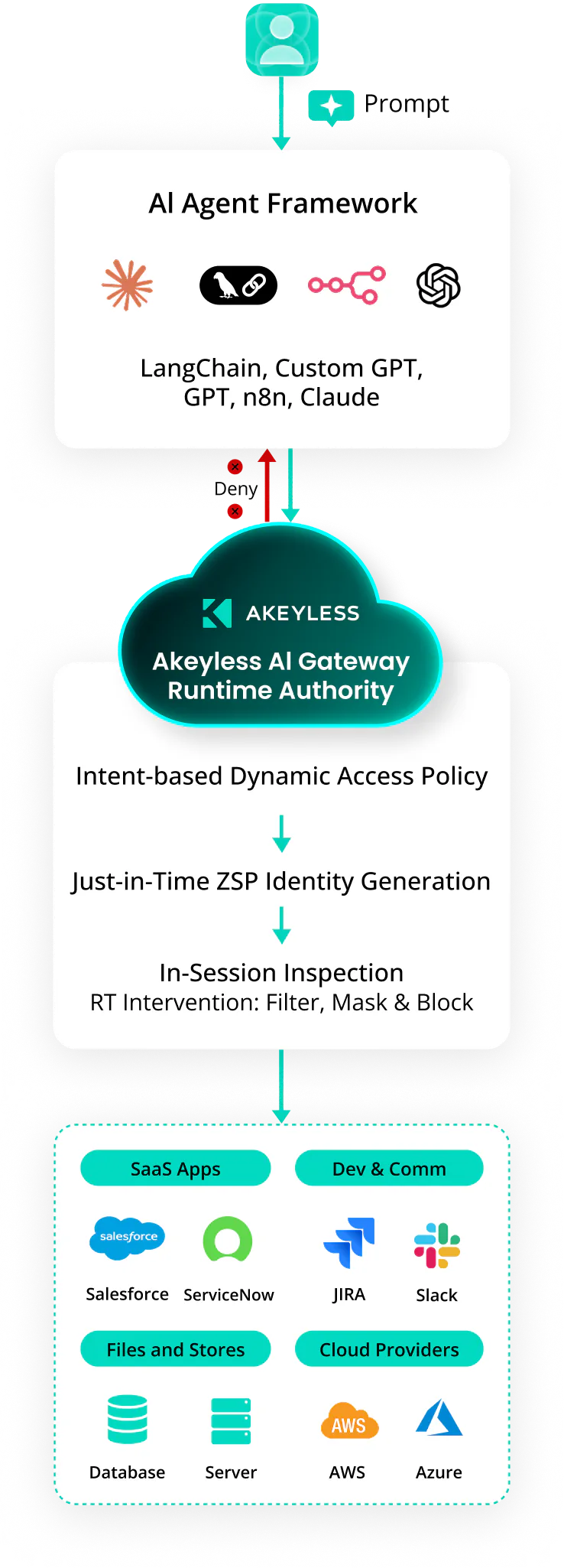
How Akeyless Secures AI Agents
Continuously discover, govern, and track agents through three components that operate as a perpetual control loop.
Agentic Runtime Authority In Action
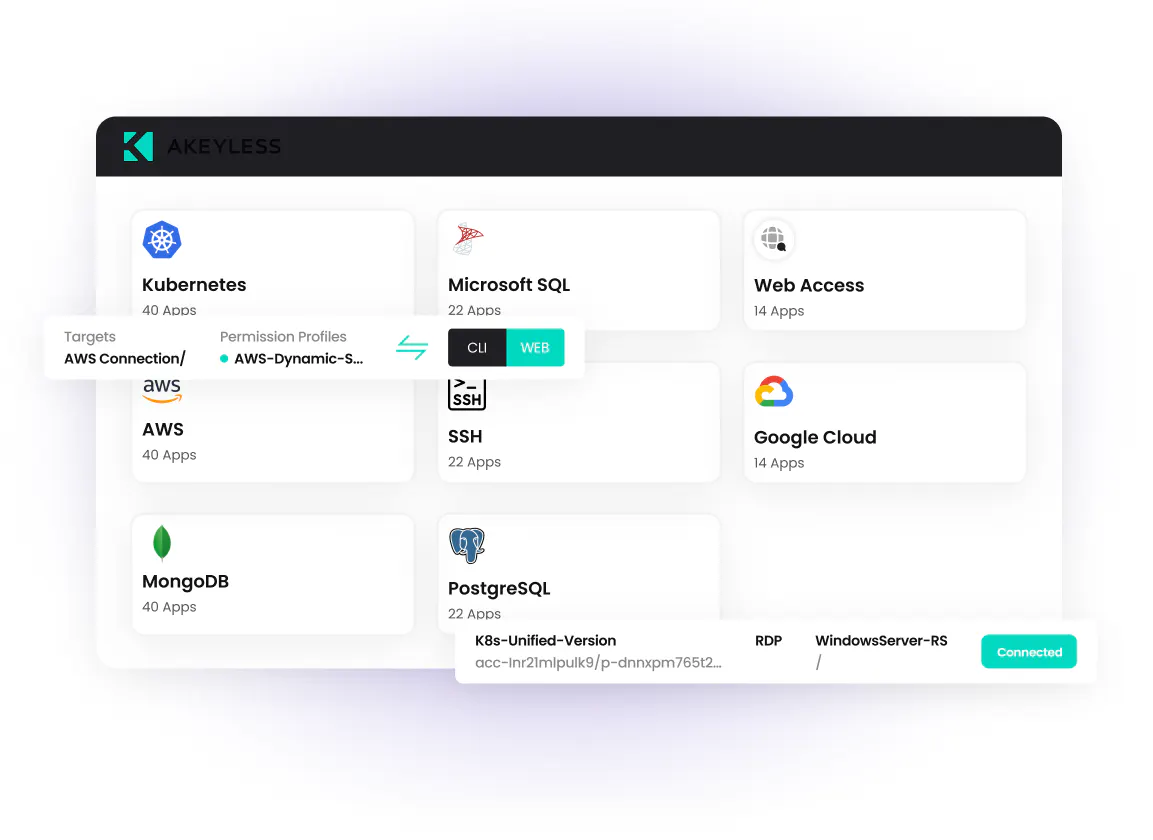
Every agent request is intercepted before reaching its target, evaluated against declared intent, and continuously inspected during execution. Live commands across SSH, databases, Kubernetes, and cloud APIs are monitored and blocked immediately if they exceed approved authority.
With Agentic Runtime Authority, you don't just hope your AI behaves. You enforce its boundaries at the Gateway level, and you maintain a tamper-proof forensic audit trail of every single prompt and API call it attempts to make.
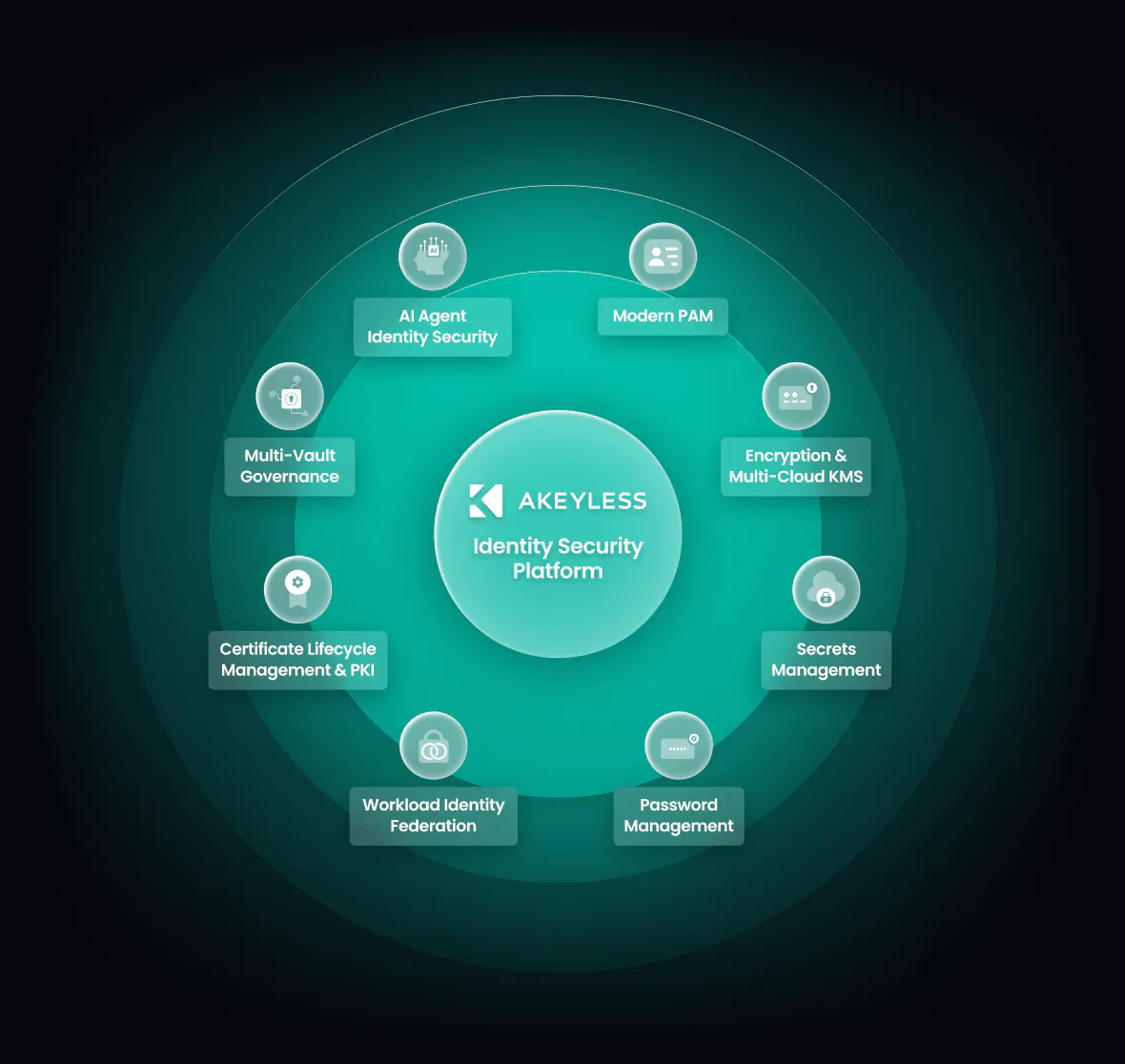
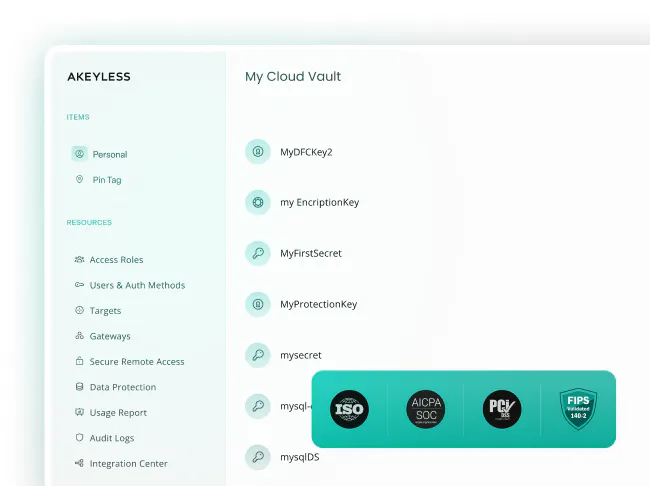
One Platform. Every Identity Secured. Everywhere.
AI agent security does not exist in isolation. The same identities and credentials that power AI agents also underpin application secrets, encryption keys, service accounts, certificates, and human access.
Akeyless unifies Privileged Access, Secrets Management, KMS, and Certificate Lifecycle Management into a single SaaS platform with one policy engine and one audit trail.
Related Resources
FAQs
Answers to the Most Common Questions About Identity Security for AI Agents