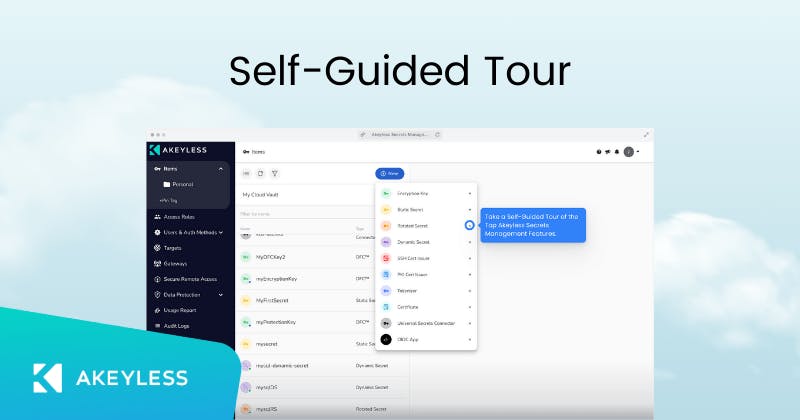
Third Party Access
Eliminate standing privileges and keep external access temporary
Provide third party access without compromising your security.
- Peace of mind: third parties only have the access they need, when they need it
- Prevent hacks by eliminating standing privileges
- Cover all the bases with a comprehensive record of all actions taken by third parties
- Save time and frustration with an easy-to-use interface that streamlines third party credential management
Features
- Provide Just-in-Time access for third parties with automatic expiration
- Integration with Identity Providers for easy authentication
- Complete tracking and auditing
- Session recordings of any access and secret use
-
Integrations
The Akeyless platform includes out-of-the-box integrations with all the tools your team uses on a daily basis
-
Auditing and Compliance
Akeyless puts security and compliance with international standards at the heart of our service
-
Unique Technology
Akeyless is built on a patented technology that ensures our customers’ data is always secure and encrypted