February 23, 2026
Posted by Suresh Sathyamurthy
Cybersecurity has entered a new era, but much of Privileged Access Management (PAM) is still operating in the past.
As organizations accelerate cloud adoption, automate infrastructure, and deploy AI-driven systems, the nature of privileged access has fundamentally changed. Identities are no longer just human administrators logging into servers. Today, machines, workloads, APIs, and AI agents outnumber human users by a wide margin — representing up to 85% of identities in many environments.
Yet many PAM solutions were not designed for this reality. A recent Gartner report found that legacy models expose organizations to regulatory risks, potential outages and security vulnerabilities. To secure modern infrastructure, the world needs a new approach, what we can call Gen 3 PAM.
The Evolution of PAM
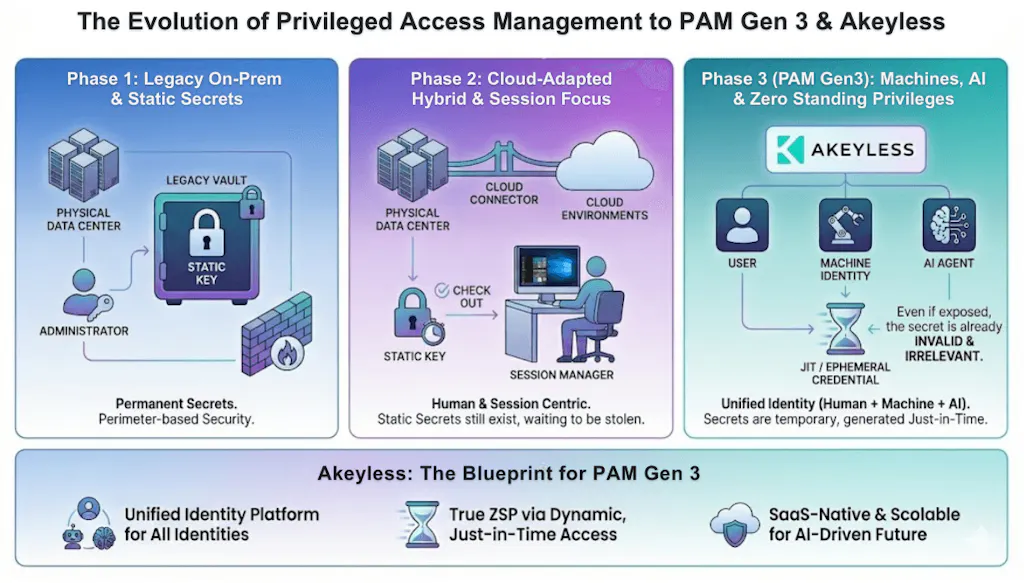
Privileged Access Management has evolved in generations, each responding to shifts in IT architecture.
Gen 1 PAM: Built for On-Prem and Legacy Systems
The first generation of PAM solutions focused on securing privileged accounts in traditional, on-premises environments. Vaulting and manual controls were sufficient for static infrastructure.
But these tools struggled with scalability and weren’t built for distributed, dynamic systems.
Gen 2 PAM: Cloud-Aware, Still Human-Centric
As organizations moved to the cloud, PAM expanded to support hybrid environments. Session monitoring, static secret management, and improved automation became standard .
However, Gen 2 PAM remained largely human-focused. It still relied heavily on persistent credentials which, if exposed, could become critical vulnerabilities.
This approach created a dangerous gap: while infrastructure evolved, privileged access remained static.
The Security Reality: Static Secrets Are the New Attack Surface
Today’s threat landscape makes one fact painfully clear:
Standing privileges and static secrets are prime targets for attackers.
Persistent credentials create opportunity. They can be exfiltrated, reused, and sold. Worse, they often remain active long after their original purpose has expired.
Meanwhile, the identity landscape has exploded. Machines, services, containers, pipelines, and AI agents now operate autonomously across multi-cloud environments .
Traditional PAM tools, built for earlier generations, struggle to unify and secure this complexity without heavy infrastructure or fragmented point solutions.
The consequences are already evident. Over 50% of organizations have experienced a security incident tied to compromised machine credentials.
This is why Gen 3 PAM has become essential.
But privileged access does not exist in isolation. The same credentials that power administrator sessions also underpin application secrets, encryption keys, service accounts, certificates, and now AI agents. In modern environments, these identity layers converge. Securing privileged access therefore requires aligning PAM with a broader identity security architecture.
What Is Gen 3 PAM?
Gen 3 PAM represents a fundamental shift in how privileged access is granted and controlled. It is:
- Inclusive of humans, machines, and AI agents
- Built around Zero-Standing Privileges (ZSP)
- Designed for just-in-time access and ephemeral secrets
- Compatible across on-prem, cloud, and legacy systems
Instead of granting long-lived access, Gen 3 PAM enforces:
- Secretless authentication
- Dynamic credential issuance
- Immediate expiration after use
- Continuous least-privilege enforcement
In short, access exists only when needed and disappears when it’s not. This completely changes the economics of risk as ephemeral secrets are useless to attackers if compromised.
Learn more about modern PAM solutions and see it in action in this blog and demo video by popular IAM expert Sam Gabrail.
Three macro trends make this shift essential:
1. The Explosion of Non-Human Identities
Human administrators are no longer the majority. Machines and AI agents now dominate cloud-native environments.
If your PAM strategy doesn’t treat non-human identities as first-class citizens, it is incomplete.
2. AI Agents Require Guardrails
AI systems increasingly operate autonomously — accessing data, triggering workflows, interacting with infrastructure.
Without Zero-Standing Privileges, AI agents become high-value, high-risk identities.
Modern PAM should apply least privilege and just-in-time controls to AI operations, not just to people.
3. Hybrid and Multi-Cloud Complexity
Organizations cannot “rip and replace” legacy systems overnight. Modern PAM must bridge on-prem, legacy, and cloud-native environments seamlessly.
Security cannot come at the cost of operational friction.
Just as importantly, it must remove infrastructure burden entirely. Appliance-based and self-managed vault solutions introduce hidden operational costs, maintenance overhead, and scaling complexity. A SaaS-native architecture eliminates servers, clusters, and manual upgrades, reducing total cost of ownership while improving resilience.
The Core Requirements of Gen 3 PAM
A true modern approach must deliver:
Zero-Standing Privileges (ZSP)
Secrets and access must be ephemeral and expire immediately after use.
Unified Identity Security
Humans, machines, and AI agents must be governed under a single framework.
A modern solution should also consolidate privileged access, secrets management, encryption key management (KMS), and certificate lifecycle management under a single control plane, with one policy engine and one audit trail, eliminating fragmented point solutions.
Secretless and Dynamic Access
Access should be federated, just-in-time, and never dependent on persistent credentials.
SaaS-Native Scalability
Infrastructure-heavy, on-prem-only tools cannot keep pace with modern distributed systems.
Why Akeyless Is Built for the Gen 3 PAM Era
Gen 3 PAM is not just a concept. It requires purpose-built architecture. Akeyless delivers a Zero-Knowledge, SaaS-native platform that unifies secrets management, access control, and encryption in a single solution.
Akeyless Modern PAM is delivered as part of this broader identity security foundation. Organizations may begin with privileged access modernization, while extending into secrets management, encryption, certificate lifecycle, or AI agent identity over time. The architecture supports modular adoption without sacrificing unified governance.
Unlike traditional SaaS or vault-based PAM solutions, Akeyless enforces Zero-Knowledge cryptography by design. Through patented Distributed Fragments Cryptography™ (DFC), encryption keys are split into fragments, ensuring no single party, not even Akeyless, can reconstruct or access customer secrets. Security is enforced cryptographically, not by trust.
Here’s how it provides the foundational capabilities required for Gen 3 PAM:
1. Comprehensive Identity Coverage
Akeyless secures:
- Human users with automated password generation and rotation
- Machines through Workload Identity Federation and ephemeral federated access
- AI agents with just-in-time, secretless authentication and continuous policy enforcement
This unified design eliminates tool sprawl and complexity.
2. True Zero-Standing Privileges
Through Distributed Fragments Cryptography™ (DFC) and zero-knowledge protection, Akeyless delivers:
- Secretless access
- Automated rotation
- Dynamic secret delivery
- Immediate expiration after use
If a credential is intercepted, it’s already useless.
3. Seamless Modern + Legacy Compatibility
Akeyless supports:
- On-prem systems
- Legacy environments
- Cloud-native infrastructure
With secure remote access, just-in-time provisioning, session monitoring, and auditing.
Organizations can evolve without disruption.
4. Innovation for the AI Era
Akeyless extends Zero-Standing Privileges to AI operations, ensuring AI agents access resources only when required and never expose long-lived secrets.
AI agents operate under the same Zero Standing Privilege model as humans and machines, with ephemeral access, continuous policy enforcement, and no persistent credentials.
It unifies these capabilities in a Zero-Knowledge framework, positioning Akeyless as a leader for the AI-powered future.
Enterprise Validation in Complex Environments
The shift to Gen 3 PAM is not theoretical. One of the world’s largest networking and infrastructure providers recently selected Akeyless to modernize privileged access across a highly complex, cloud-heavy environment. The evaluation included incumbent and category leaders, yet Akeyless was chosen based on its strong alignment with Privileged Access Management use cases, ability to support real SRE workflows, significantly better economics, and a clear roadmap commitment toward FedRAMP High, a critical requirement for government and DoD initiatives.
Unlike traditional PAM vendors that introduced operational friction, infrastructure overhead, and high cost, Akeyless delivered a single SaaS-native platform that unified Privileged Access Management and Secrets Management with faster time-to-value and architectural simplicity. The decision validated Akeyless’s ability to displace entrenched vendors in large-scale environments. and demonstrated that Gen 3 PAM is becoming the new enterprise standard.
The Bottom Line
Privileged access is no longer just an IT problem. It is an existential security challenge in a world driven by cloud, automation, and AI.
Static secrets are liabilities.
Standing privileges are risk.
Human-only PAM is obsolete.
The transition to Gen 3 PAM isn’t optional. It’s inevitable.
Akeyless replaces vaults, passwords, and standing privileges with Zero-Knowledge, identity-based access for humans, machines, and AI. Gen 3 PAM is delivered as part of a broader identity security platform that unifies privileged access, secrets management, PKI, encryption key management, and identity visibility under one SaaS control plane.Ready to eliminate standing privileges and modernize privileged access? Request a demo to see Akeyless Gen 3 PAM in action.
