March 3, 2026
Posted by Or Amar
Most AppSec programs fail because they prioritize dashboards over developer velocity. When you bury teams under a mountain of noise and punish developers for legacy debt they didn’t even write, you don’t get security – you get friction.
This isn’t a product announcement. It’s how we run Application Security internally at Akeyless. As our engineering velocity increased, traditional scanning models couldn’t keep up. We needed a system that scales with developers, not against them.
At Akeyless, we built an AI-driven security control layer that reduces noise by gating only what truly increases risk. We’re moving beyond the “Alert Factory” into a continuous, automated loop that starts in the IDE and ends with Autopilot Remediation. No more hunting through dashboards; just a clean path from code to merge.
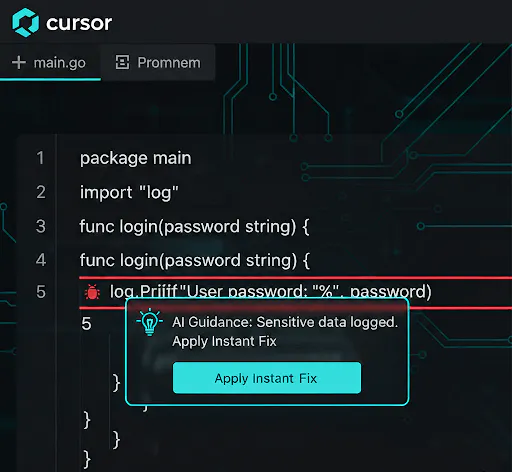
1. Cursor‑Time: The Secure Authoring Flow
The best PR gate is the one you never hit. Before a developer even creates a commit, we bring security into the authoring workflow inside Cursor.
- Authoring Guardrails: We analyze the code structure as you write it. If you’re using an insecure pattern or an unverified third-party package, we flag it in real-time.
- Instant Fixes: AI guidance runs locally to help you refactor risky code or fix secrets hygiene issues without ever leaving your flow.
The Result: We remove the bulk of friction. By the time code reaches a PR, the obvious “foot-guns” are already gone.
2. The PR Layer: Unified Validation
When a Pull Request is opened, we trigger a validation suite that moves beyond surface-level scanning. We provide a transparent, evidence-based gate across four core areas:
- Logic & Custom Code: We identify complex vulnerabilities, such as authorization bypasses, specifically within your unique business logic.
- Supply Chain: We interrogate every library for known exploits and determine if the vulnerable code is actually reachable in your app.
- Environment & Config: We verify all configuration files – Terraform, K8s, Helm, and even Dockerfiles – against your live environment to ensure networking and permissions follow Least-Privilege.
- Integrity & Provenance: We generate an SBOM and verify that the code validated in the PR is exactly what gets deployed to production.
The Result: Security is no longer a “black box” – pass/fail check. It’s an actionable gate that gives developers the full context of how their changes impact the system.
3. Integration Power: The Ecosystem Control Plane
Akeyless doesn’t work in a vacuum. We act as the orchestration layer for the entire security stack. We integrate deep security checks with the industry’s biggest players to provide a “Single Pane of Truth”:
- Cloud & Runtime: Deep correlation with Wiz and Prisma Cloud.
- Artifacts & Scanning: Seamless workflows with JFrog, Aqua Security, and Snyk.
- Deterministic Governance: Our AI Agents pull deterministic signals from these platforms, ensuring that “Pass/Fail” status is based on live environmental data, not just static rules.

4. The Delta Engine: Trust Through Fairness
The fastest way to destroy developer trust is to fail PRs for issues the PR did not introduce. We gate on the Delta. In practice, this reduces unnecessary PR failures significantly in our internal pipelines, without increasing risk exposure.
- Contextual Baselines: We snapshot your environment’s state before the commit. If a vulnerability existed yesterday, we track it, but we don’t block your merge today.
- “You Break It, You Fix It”: We only gate on newly introduced High or Critical risks. This keeps the pipeline moving while preventing the attack surface from expanding.
- Backlog Independence: This approach makes security scalable immediately, allowing you to improve security posture without requiring a massive, multi-month backlog cleanup first.
5. Remediation‑Time: Moving Toward Autopilot
Detection without action is just a tax. The system is designed to move from “detect & gate” into “fix & ship”. Agents propose fixes, they don’t bypass review. Every change is transparent, explainable, and developer-approved:
- Total Code Hardening via AI Agents: Whether it’s a logic flaw in your application or a configuration error, dedicated AI Agents identify the exact line and generate a ready-to-merge patch. You aren’t just told “this is wrong”; the agent delivers the “right.”
- Agentic Dependency Upgrades: Instead of just flagging a vulnerable library, AI Agents calculate the safest upgrade path. The agent proactively opens a PR that bumps the version to the first non-vulnerable release that won’t break your existing builds.
- Instant Configuration Fixes: If a developer checks in a file with broad permissions or insecure defaults, an AI Agent automatically generates a “hardened” version of that file. The developer simply hits “Approve” to let the agent swap the insecure code for the secure version.
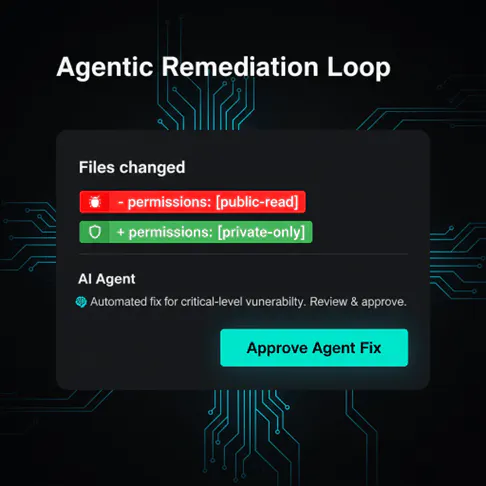
The Endgame: Continuous Protection
The future of AppSec isn’t a bigger dashboard. It’s a system that guides developers in the IDE, enforces policy fairly in PRs, and continuously drives remediation.
That’s how we approach AI‑native AppSec at Akeyless: not as a gate, but as a continuously improving system. Less noise. Fewer blind spots. Faster remediation.
Moving from alerts to autopilot, without losing control.






