
Product Updates | Security
Akeyless Achieves FIPS 140-3 Validation: What It Is and Why It Matters
Akeyless achieves FIPS 140-3 validation for its cryptographic module (#5227), strengthening identity security, compliance, and post-quantum readiness.

Product Updates | Security
Akeyless achieves FIPS 140-3 validation for its cryptographic module (#5227), strengthening identity security, compliance, and post-quantum readiness.
AI | Machine IAM | Security
Competitor | DevOps | InfoSec
AI | Security

Product Updates | Security
Akeyless Achieves FIPS 140-3 Validation: What It Is and Why It MattersAkeyless achieves FIPS 140-3 validation for its cryptographic module (#5227), strengthening identity security, compliance, and post-quantum readiness.
AI | Machine IAM | Security
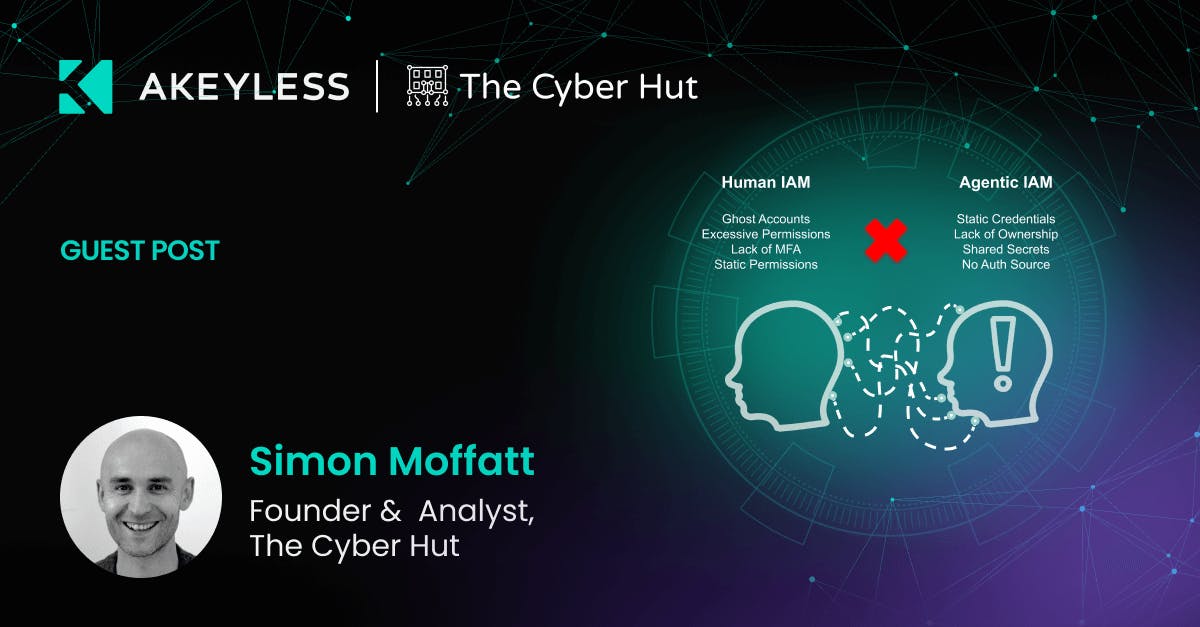
AI Agents and Machines Can’t Keep SecretsGartner’s latest research explains why traditional approaches to securing machine identities are failing, and how organizations can move toward identity-based access to reduce risk.

Competitor | DevOps | InfoSec
Akeyless vs. Infisical: Enterprise-Grade Secrets Management for the AI and Cloud EraSee how Akeyless Modern PAM outpaces Delinea with a unified, Zero-Knowledge SaaS platform built for automation, scalability, and modern PAM use cases.

AI | Security
Mitigating OWASP Agentic AI Risks with Identity ControlsArtificial intelligence is rapidly evolving from simple assistants into autonomous AI agents capable of executing real tasks across infrastructure, data platforms, and SaaS systems. These agents retrieve information, call APIs, access databases, and orchestrate workflows without direct human supervision. While this shift unlocks tremendous productivity, it also introduces an entirely new security challenge: how to […]

DevOps | Security
Best Practices For Managing Secrets Across Multiple EnvironmentsLearn how to manage secrets securely across multiple environments. Explore best practices, tools, and strategies for protecting sensitive information in modern systems

InfoSec | Security
Top Secrets Management Tools For ComplianceExplore the leading secrets management tools that help your organization stay compliant, secure credentials, automate rotation, and maintain audit trails.

InfoSec | Security
How to Secure Secrets in Cloud Environments: Key StrategiesLearn how to manage secrets securely in cloud environments. Discover best practices, tools, and strategies to protect sensitive data in the cloud.

Competitor | Security
Akeyless Multi Vault Governance for HashiCorp Vault and Cloud Secrets ManagersAkeyless multi vault governance simplifies secrets management by enabling bidirectional sync, automated rotation, and centralized control across Azure, Vault, and databases.

Product Updates
Akeyless Password Manager: Now With a Secure Browser ExtensionEnterprises adopt password managers to solve real problems: secure password sharing, centralized generation policies, role-based access control, compliance visibility, and lower operational cost. But as cloud, hybrid, and multi-team environments grow, legacy tools struggle to scale. Akeyless Password Manager now brings enterprise-grade password and secrets management directly into the browser with a new browser extension, […]
AI
From Anonymous to Accountable: Giving AI Agents a Digital IdentityRise of Agents & Why They’re Different AI-driven automation has accelerated rapidly over the past year, delivering unprecedented productivity and business agility across industries and sectors. The benefits are both broad and considerable. Nearly all areas – across both the public and private sectors are experiencing increased adoption of agentic-AI capabilities. However this has brought […]

AI | Tech Tips
From Alerts to Autopilot: Building AI‑Native AppSecPractical tips for AI-native AppSec, including shifting security into the IDE, gating on real risk, and using automation to propose fixes. A look at how we approach it at Akeyless and ideas you can apply to your own pipelines.

Machine IAM
Why the World Needs Modern PAMPrivileged access is evolving. Learn how Gen 3 PAM eliminates standing privileges and secures humans, machines, and AI with unified identity security.
Discover how Akeyless simplifies secrets management, reduces sprawl, minimizes risk, and saves time.
Take a self-guided tour of our top features.
See the platformLearn what Akeyless can do for your team.
Talk to an expert