
InfoSec | Security
Simplifying Secrets Management for Compliance (DORA, C5, and NIS2)Explore how secrets management can help tackle the compliance challenges of DORA, C5, and NIS2, streamlining processes and reducing risks while enhancing security.

InfoSec | Security
Simplifying Secrets Management for Compliance (DORA, C5, and NIS2)Explore how secrets management can help tackle the compliance challenges of DORA, C5, and NIS2, streamlining processes and reducing risks while enhancing security.

InfoSec | Security
Why Identity-Based Attacks Are on the Rise: Insights from Former CISO of Caterpillar FinancialWhy are identity-based attacks on the rise, and what can CISOs do to stop them? In this fireside chat, Ross Young, former CISO of Caterpillar Financial, shares insights with Akeyless CEO Oded Hareven on securing machine identities, managing secrets, and staying ahead of evolving cyber threats.

DevOps | InfoSec
Beyond Silos: How to Streamline Secrets Management Across PlatformsThis blog explores the challenges of vault sprawl, including its impact on security, cost, and complexity, and offers actionable solutions for managing secrets across environments, whether through consolidation or centralized visibility.

DevOps | InfoSec
The Rise of Machine Identities: Admiral Mike Rogers Discusses the Next Cybersecurity FrontierDiscover key insights from a fireside chat between Akeyless CEO Oded Hareven and Admiral Mike Rogers, former NSA Director, as they explore the challenges of machine identity management and innovative strategies to simplify and secure the future of cybersecurity.

DevOps | InfoSec
Secure Your Secrets with Automated Rotation—Here’s Why It MattersThis blog explores the critical role of secrets rotation in securing credentials and workload identities, highlights real-world breaches, and provides actionable insights into automated solutions and best practices for effective secrets management.
DevOps | Security
A Platform Engineering Guide to Managing Secrets with AkeylessPlatform engineering equips development teams with efficient and secure workflows to streamline code deployment at scale. This guide explores the essentials of platform engineering, the value of Internal Developer Platforms (IDPs), and how secrets management plays a crucial role. Learn how Akeyless can simplify secrets management for multi-cloud setups, enhance security with dynamic secrets, and integrate seamlessly into your workflows.

News
Akeyless secures strategic investment from Deutsche BankAkeyless, an innovator in the identity security market, today announced a strategic investment from Deutsche Bank’s Corporate Venture Capital (CVC) group.

InfoSec | Security
Building vs. Buying Secrets Management: What’s Right for You?This blog explores the pros and cons of building vs. buying a secrets management solution, helping DevOps and InfoSec teams make informed decisions on security, scalability, and compliance. Discover which option best suits your organization’s needs.

Security
Embracing a Secretless Approach with AkeylessManaging usernames and passwords has become an increasing challenge in today’s highly automated, multi-cloud, and microservice environments. From a security perspective, the greatest challenge is long-lived credentials that can be compromised. This is where Akeyless and its secretless approach come in, promising a robust and scalable solution for Secure Remote Access (SRA) – also known […]

News
Introducing the World’s First Akeyless Unified Secrets and Machine Identity PlatformIntroducing the Akeyless Unified Secrets & Machine Identity Platform. The platform transforms cybersecurity by addressing the leading cause of breaches—compromised credentials and machine identities—through a fully integrated, cloud-native solution.
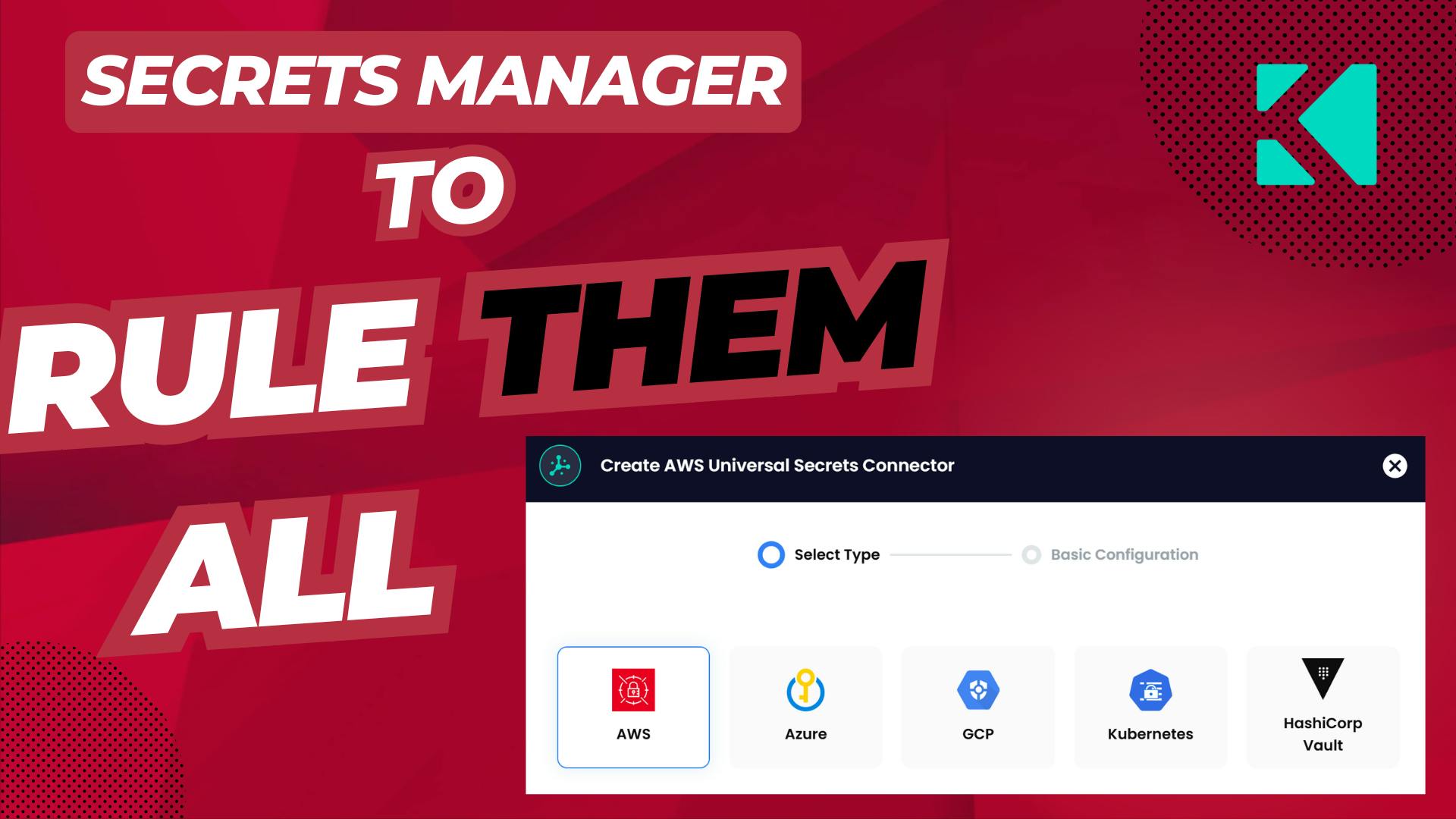
DevOps | InfoSec | Security
Centralized Secrets Management: Eliminate Silos with Akeyless Universal Secrets ConnectorAs organizations adopt hybrid cloud environments, secrets management has become critical to security and operational efficiency. Platform engineers often seek to centralize secrets management with a single tool, but development teams may be tied to specific options like AWS Secrets Manager or Google Secret Manager due to unique requirements. Akeyless Universal Secrets Connector (USC) unites all your secrets managers, solving the chaos with a single access point—without forcing migration. By providing a centralized platform, Akeyless USC simplifies administration, enhances security by enforcing consistent policies, and boosts productivity across the enterprise.

DevOps | InfoSec
Protecting Machine Identities: The Overlooked Cybersecurity CrisisWhy enterprises must act now to secure mission-critical systems. We live in unprecedented times. In the last month, I was notified by Ticketmaster,Change Healthcare, and Pentester.com that my credit card, health care, and socialsecurity details were compromised. Taking the advice of Pentester, I froze my credit andI’m glad I did. Today, I received a letter […]




Discover how Akeyless simplifies secrets management, reduces sprawl, minimizes risk, and saves time.
Take a self-guided tour of our top features.
See the platformLearn what Akeyless can do for your team.
Talk to an expert