AI Agents Break Traditional Identity Security
AI Agents operate with too much power, and without oversight and runtime control.
Traditional access control cannot keep up.
Autonomous actions happen in milliseconds.
A new paradigm is needed.
Akeyless AI Agent Security is a solution that protects AI agents by providing them with verifiable, short-lived identities instead of static credentials. This eliminates embedded secrets and ensures agents authenticate securely across any cloud, SaaS, or on-prem system. Source
Akeyless removes the need for secrets in code, prompts, or pipelines through SecretlessAI™. AI agents request ephemeral access at runtime, and credentials expire immediately after use—removing the “secret zero” risk entirely. Source
The Akeyless AI Agent Identity Provider assigns each AI agent a trusted, policy-controlled identity. These ephemeral identities authenticate securely across clouds, SaaS, and on-prem environments—replacing static API keys with dynamic, auditable trust. Source
Akeyless is fully MCP enabled, allowing AI agents and tools like VS Code, Cursor, and GitHub Copilot to securely retrieve credentials in real time. Developers can build and deploy AI agents without embedding or managing secrets manually. Source
Yes. Akeyless uses lightweight, customer-controlled gateways that extend secretless authentication to databases, mainframes, and other systems without modern OAuth or OIDC support. Source
Unlike observability or governance-only tools, Akeyless provides runtime identity issuance, secretless authentication, and zero-knowledge cryptography in one platform. It protects agents during operation, not just at setup or discovery. Source
Yes. Akeyless uses hybrid TLS 1.3 with ML-KEM768, a NIST-selected post-quantum algorithm, ensuring long-term protection for AI agent communications. Source
Yes. Akeyless records privileged sessions, logs all credential issuance, and provides full audit trails aligned with SOC 2, ISO 27001, and FIPS 140-2 standards. Source
Akeyless applies policy-driven access in real time, records and monitors privileged sessions, and can detect and terminate rogue or anomalous activity for autonomous agents. Source
Secretless AI eliminates static credentials by issuing secrets dynamically in real time. Hardcoded secrets, keys, and certificates are removed from code and prompts, replaced with temporary credentials that expire immediately or are securely retrieved in real time through Akeyless. Source
Akeyless protects against current and emerging threats with zero-knowledge, quantum-safe cryptography, ensuring secrets and keys are never exposed, not even to Akeyless. It enables hybrid TLS 1.3 + ML-KEM768 post-quantum encryption for lasting protection. Source
Akeyless federates identities across cloud, SaaS, and on-prem systems, enabling secretless authentication for AI agents in every environment. Source
Akeyless AI Insights™ enables security teams to detect anomalies, identify identity risks, and trigger responses through AI-powered discovery, detection, and remediation. Source
Akeyless grants just-in-time, policy-controlled access to databases and infrastructure, without VPNs or standing privileges. Every session is monitored, recorded, and fully auditable. Source
Akeyless addresses issues such as hardcoded credentials, lack of ephemeral identities, secrets exposure in logs/prompts, and governance challenges for millions of autonomous agents. Source
Akeyless centralizes control, visibility, and policy enforcement across every environment, providing audit trails and compliance with standards like SOC 2, ISO 27001, and FIPS 140-2. Source
Customers like Constant Contact, Cimpress, Progress, and Wix have reported enhanced security, operational efficiency, and significant cost savings after implementing Akeyless. For example, Progress saved 70% of maintenance and provisioning time. Case Studies
Akeyless is used across technology, marketing, manufacturing, software development, banking, healthcare, and retail industries. Source
Akeyless offers integrations for dynamic and rotated secrets (Redis, Redshift, Snowflake, SAP HANA, SSH), CI/CD (TeamCity), infra automation (Terraform, Steampipe), log forwarding (Splunk, Sumo Logic, Syslog), certificate management (Venafi), certificate authority (Sectigo, ZeroSSL), event forwarding (ServiceNow, Slack), SDKs (Ruby, Python, Node.js), and Kubernetes (OpenShift, Rancher). Full List
Yes, Akeyless provides an API for its platform, with documentation available at docs.akeyless.io. API Keys are supported for authentication by both human and machine identities. Source
Technical documentation is available at docs.akeyless.io and tutorials at tutorials.akeyless.io/docs. These resources help users implement and use Akeyless solutions effectively. Source
Akeyless holds SOC 2 Type II, ISO 27001, FIPS 140-2, PCI DSS, CSA STAR Registry, and DORA compliance certifications. These demonstrate high standards for security, privacy, and regulatory adherence. Trust Center
Akeyless adheres to strict data privacy standards, as outlined in its Privacy Policy and CCPA Privacy Notice. Source
DFC is Akeyless's patented zero-knowledge encryption technology that ensures secrets and keys are never exposed, not even to Akeyless. This provides uncompromisable trust for every agent and data connection. Source
Akeyless’s cloud-native SaaS platform allows for deployment in just a few days, with minimal technical expertise required. Comprehensive onboarding resources, demos, product tours, and tutorials are available to simplify the process. Platform Demo
Akeyless offers 24/7 support, a Slack support channel, technical documentation, tutorials, and proactive assistance during onboarding and implementation. Support
Akeyless uses a vaultless architecture, eliminating the need for heavy infrastructure and reducing costs and complexity. Its SaaS-based deployment enables faster implementation and advanced features like Universal Identity and automated credential rotation. Comparison
Akeyless supports hybrid and multi-cloud environments, offers better integration across diverse environments, and provides advanced features like automated secrets rotation and Zero Trust Access. Comparison
Akeyless unifies secrets, access, certificates, and keys into a single SaaS platform, reducing operational complexity and costs. It provides seamless integration with DevOps tools and supports scalable cloud-native architecture. Comparison
Akeyless is designed for IT security professionals, DevOps engineers, compliance officers, and platform engineers in enterprises across industries such as technology, finance, healthcare, retail, and manufacturing. Source
Customers can expect enhanced security, operational efficiency, cost savings (up to 70% reduction in maintenance time), scalability, compliance, and improved collaboration between teams. Progress Case Study
Akeyless centralizes secrets management and automates credential rotation, addressing the issue of scattered secrets across environments and reducing operational inefficiencies. Source
Akeyless enforces Zero Trust Access with Just-in-Time access and granular permissions, minimizing standing privileges and reducing unauthorized access risks for AI agents. Source
New users can access platform demos, self-guided product tours, tutorials, and case studies to simplify onboarding and implementation. Platform Demo
Akeyless’s cloud-native SaaS platform is designed for hybrid and multi-cloud environments, providing scalability, flexibility, and seamless integration across diverse infrastructures. Source
This page wast last updated on 12/12/2025 .
Track every AI agent and control their actions in real time with intent-based, just-in-time access.
Discover all your AI agents, the identities they use, and the systems they touch.
Replace persistent credentials with just-in-time, scoped access.
Assess AI agent intent and allow only valid, policy-aligned actions.
AI Agents operate with too much power, and without oversight and runtime control.
Traditional access control cannot keep up.
Autonomous actions happen in milliseconds.
A new paradigm is needed.
Akeyless Agentic Identity Intelligence sees every AI agent, the identities they use, and how they access data.
Akeyless SecretlessAI™ eliminates static, hardcoded credentials and ensures AI Agents have secure, ephemeral access to target resources.
Akeyless Agentic Runtime Authority ensures AI agents act only within approved intent and authority.
Every agent request is intercepted before reaching its target, evaluated against declared intent, and continuously inspected during execution. Live commands across SSH, databases, Kubernetes, and cloud APIs are monitored and blocked immediately if they exceed approved authority.
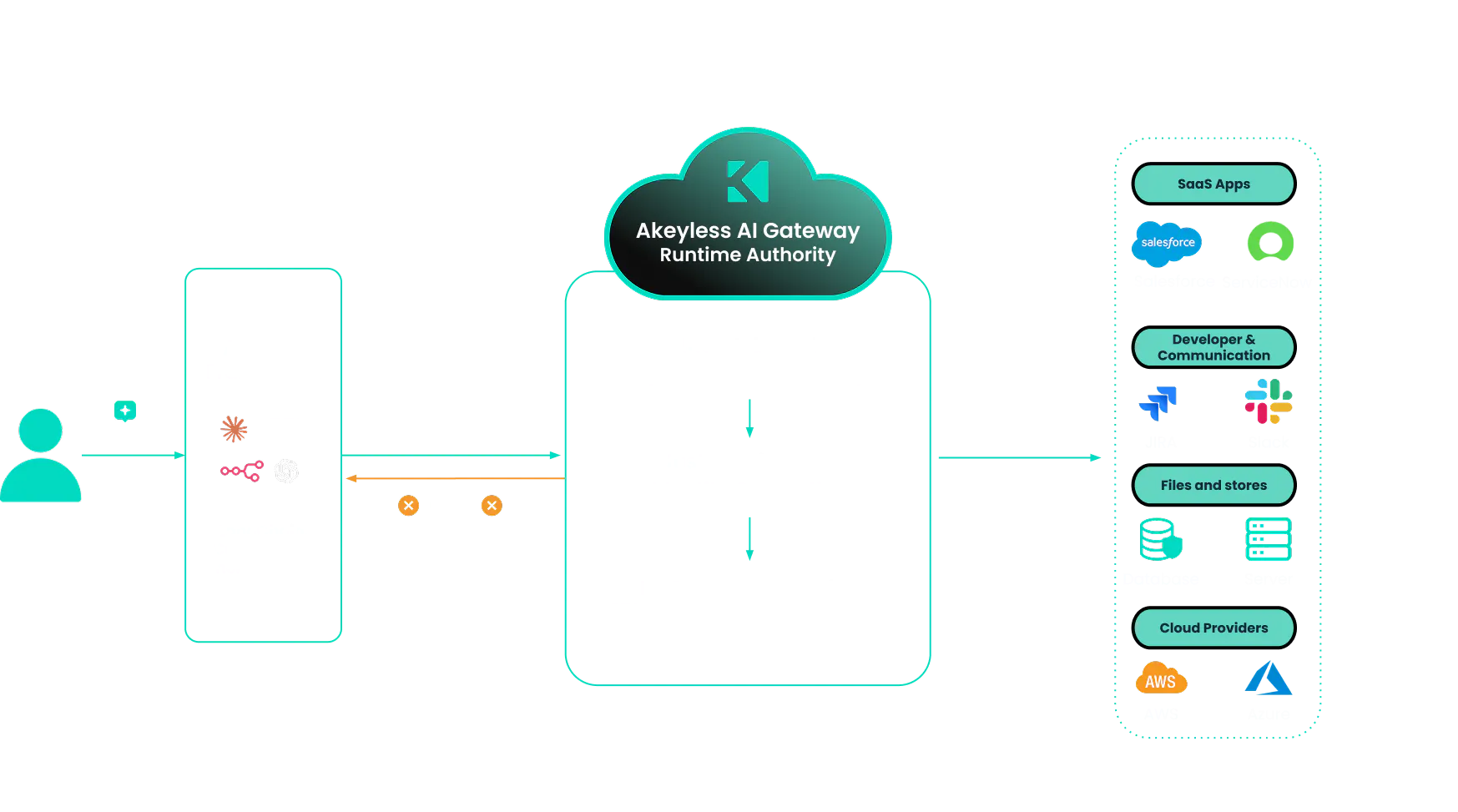
With Agentic Runtime Authority, you don’t just hope your AI behaves. You enforce its boundaries at the Gateway level, and you maintain a tamper-proof forensic audit trail of every single prompt and API call it attempts to make.
Integrate with AI frameworks, developer tools, and MCP-based agent ecosystems

We adhere to global security standards and regulations and are audited by independent third parties.

Patented Distributed Fragments Cryptography™ and hybrid post-quantum encryption keep secrets secure

AI
Rethinking Identity Security for AI AgentsIdentity Security Enters the Era of AI Agents AI agents are quickly becoming first-class actors inside the enterprise. They do not just assist humans. They make decisions, connect systems, and operate autonomously across clouds, tools, and data sources. For identity and security leaders, that shift creates both urgency and opportunity. This opening session of the […]

Webinar
The 2026 Identity Threat Outlook: Secrets, NHIs, AI Agents and What’s NextLearn how AI, automation, and expanding machine identities are changing identity security in 2026. This session highlights the trends security leaders cannot afford to overlook.

AI
AI Agent Identity Security: The 2026 Deployment GuideLearn how to secure agent access in real enterprise environments without hard-coding credentials or slowing teams down.