Posted by Simon Moffatt
March 5, 2026
Rise of Agents & Why They’re Different
- Increase and Benefits of Use
- Complex Characteristics NHI Volume, Human Behaviour
AI-driven automation has accelerated rapidly over the past year, delivering unprecedented productivity and business agility across industries and sectors. The benefits are both broad and considerable. Nearly all areas – across both the public and private sectors are experiencing increased adoption of agentic-AI capabilities.
However this has brought some considerable identity and security challenges from an operational perspective. The innovative speed of AI and agentic deployments has been rapid – whilst identity and security components are often being left behind – resulting in the poor selection of controls or the avoidance of controls entirely. Shadow-AI is likely to be considerable in many organisations as non-technical decision makers experiment with online SaaS delivered models and chatops interfaces. But why is this an issue? Why can’t agentic systems simply be managed like any other web application?
Well they exhibit a new and somewhat unique set of characteristics. If we take a brief step back and understand that identity models typically cover three-main sub-categories: identity for software, hardware and people. The people-centric area is the most mature from a technology and framework perspective, namely as that is where many commercial identity and access management (IAM) features were designed for. Workforce B2E (business to employee) single sign on (SSO), access review and then later in the early 2000s life cycle management – driven by compliance and productivity challenges.
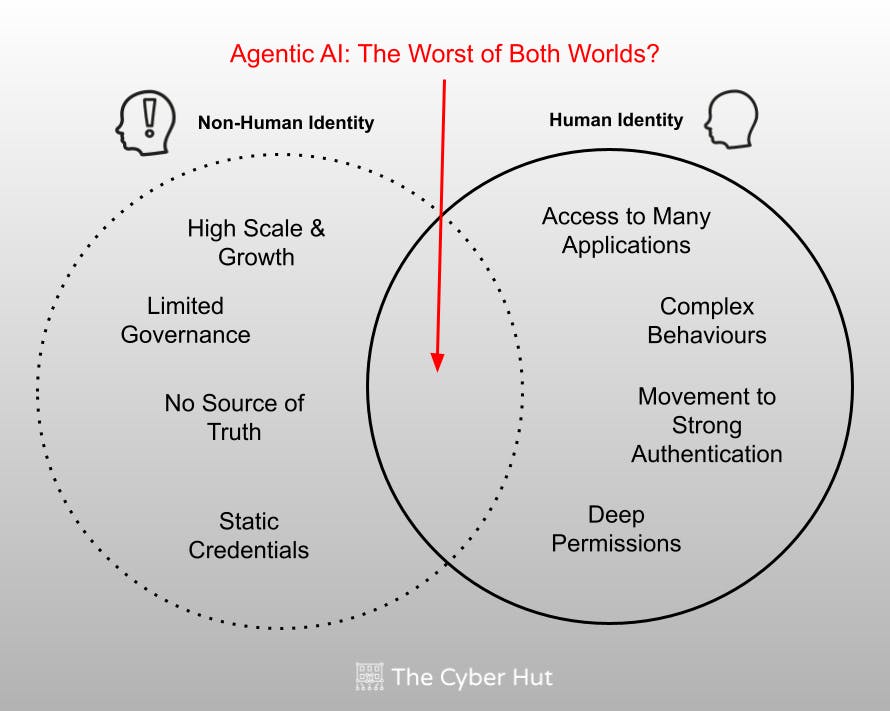
The last decade has seen the dedicated emergence of service, workload and non-human identity (NHI) tools and concepts too. NHIs have created non-functional requirements that existing human identity models cannot cope with (think volume, growth and credential rotation capacity) and create some interesting challenges themselves. For example how to replicate the assurance associated with biometric authentication to workloads?
Whilst the organizational maturity for human identity may be higher than for NHIs, organisations are still plagued with numerous human-centric IAM challenges – such as poor MFA enrolment, excessive permissions, poorly executed access review and slow cleanup operations.
To that end we start to see agentic-AI being somewhat shoe-horned between being non-human in nature, but heavily reliant on human interactions and patterns of access on the other – and often amplify the failings in deployment in both camps.
Problems With Existing Identity & Cyber Security Models
- How to Apply Strong Auth to Agents?
- Migrating from Long Lived Credentials
- Secretless AI Agents: Enabling Identity Without Secrets
We can then start to see the amplification of issues in both the human and non-human identity worlds. Excessive permissions for humans coupled with a lack of visibility for non-human identities. A lack of authoritative source for workloads, but the rapid creation and management of agentic-AI. This is creating a cascading set of access control, visibility and behaviour management problems that existing tools and models of security were not designed to cope with.
For example, from a people-centric identity point of view the concept of strong authentication is well understood. The implementation of strong authentication or MFA is still not quite complete however – and many internal and external systems still rely on shared secrets and passwords. Why? Integration complexity, service consolidation, end user behaviours and cost act as barriers to adoption – even though concepts like cryptographic challenge response and initiatives like FIDO have effectively solved the technical problem.
| Actor | Factor | Risk |
|---|---|---|
| Agentic-AI | Lack of Human Owner | Accountability |
| Agentic-AI | Static Permissions | Data Loss |
| Agentic-AI | Shared Secrets | Non Repudiation |
| Agentic-AI | Static Credentials | Incident Remediation |
The same concept can then be applied to excessive permissions, a lack of just in time access request enforcement or the removal of ghost accounts. Many security design points that are well understood but are often not entirely implemented.
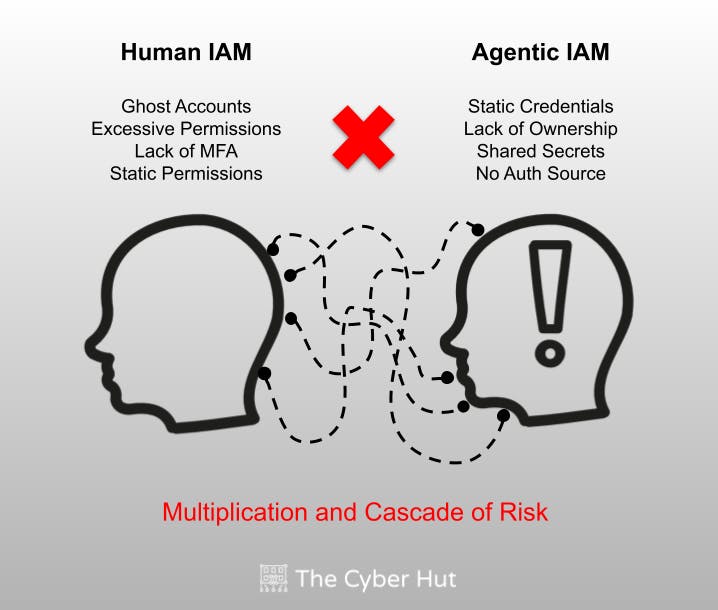
So we need to ground our analysis not just on what is needed to manage and secure the agentic world, but to also consider that the foundations for agentic security are potentially sitting on top of poor human-centric identity and access management maturity or implementation.
A cascading set of issues start to emerge, from not being able to link an agentic identity to a carbon-life form, to perhaps linking to a human identity that should actually be disabled or removed, has excessive permissions or shouldn’t even have access to the agent in the first place.
If we take some concepts from the human world that are mature in design – concepts like strong authentication, a movement away from shared secrets and centralised visibility and control – how can those concepts be adapted and implemented for the agentic-world?
A common design flaw for NHI implementations has often been the use of both shared secrets and a long-lived nature of those credentials – too often hard-coded into API-clients or reusable code blocks. Translating those poor practices into the agentic world sees a huge amplification on the impact and likelihood for both internal and external adversarial activity.
What are the alternatives? Firstly humans are migrating from a shared-secrets model (i.e. passwords and PINS) to cryptographic challenge-response concepts – why not NHI and agentic? The identification of static string-based credentials that are hard-coded and difficult to rotate should be part of any risk discovery process with the continual scanning of existing code repositories. The next stage is a migration to something more secure, scalable and short-lived.
Cryptographic Foundation and Secretless
- Improving Accountability & Repudiation
- Credential Life Cycle Management for Agents
We need to understand that credential management is a life cycle and operates within a broader ecosystem. That life cycle includes issuance and usage, but also rotation, revocation and an initial verification process – often known as the secret-zero problem. Unlike human-centric approaches to authentication where both biometric and an interactive set of stages can be utilized, the issuance (of public/private key pairs for challenge response) credentials still requires an initial verification of the NHI or agentic-identity that is requesting association to the credential.
Concepts like SPIFFE (secure production identity framework for everyone) can help here – by providing an interoperable model for processes to be attested independently during that initial credential creation and association phase – essentially making sure the correct thing gets the correct credential at the correct time.
Of course in the NHI and agentic worlds this needs to happen automatically and at scale. Then what? Well the credentials that are minted and issued – albeit likely to support strong authentication – also need to have some additional characteristics. They should be short-lived and ephemeral – either automatically expiring after a set time or task completion – or auto-rotatable – supporting an entirely repeatable and programmatic way to generate new credentials – reducing blast radius impact of credential theft and misuse.
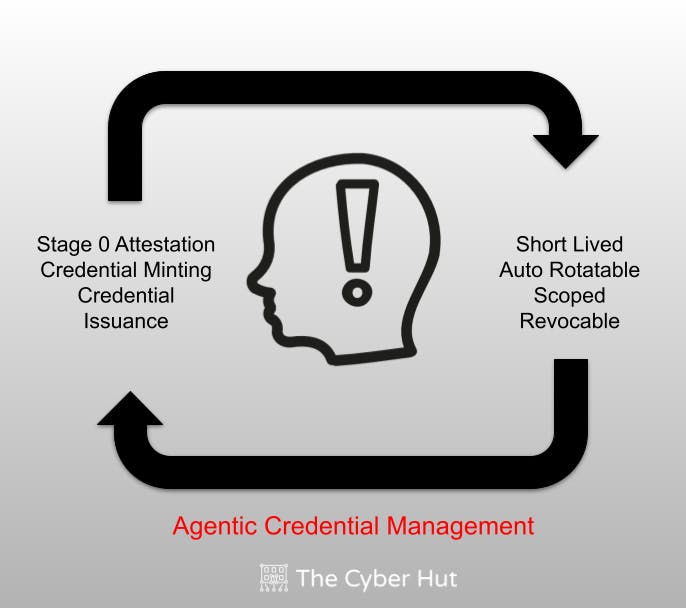
Whilst subtly different, how the credentials are used and scoped should also be considered. By this we need to gain an understanding of what the credential is being used for. What happens post authentication with respect to authorization, access control and enforcement? This should include concepts such as the principle of least privilege – assigning permissions only when needed of course, but also only assigning permissions that are needed to complete the objective that has been set.
The Road Ahead
- Discovery, Visibility and Risk Analysis
- Unified Identity Control Plane for Humans, Machines, and AI Agents
It is important to consider what can be controlled from an agentic-AI perspective. Whilst human-related risk exists and will continue to do so, understanding and then prioritizing countermeasures for agents is critical. But where does the immediate risk exist?
| Risk | Action | Goal |
|---|---|---|
| Hardcoded Secrets | Code scan for hard coded strings, secrets, keys | Move to cryptographic challenge response authentication |
| Long lived Credentials | Identify and exchange | Short lived and rotatable credentials |
| Hard coded bootstrapping | Migration to SPIFFE | Attestable processes and automatic issuance of creds |
| Distributed authentication | Migration to federated access | Centralised identity provider function for NHI/Agentic |
NHI and agentic systems are plagued with being built in a distributed and often isolated manner – resulting in an isolated and inconsistent approach to authentication and credential management. The strategic aim is to deliver a centralized identity provider model, with modern challenge response authentication that can in turn be used for downstream access control enforcement. The use of shared secrets, long lived certificates and hard-coded keys is common and should be identified for both existing deployments and new services.
The use of a cryptographic based authentication capability that can support federated access also helps deliver a more accountable identity function for agents and workloads. Unique naming, and an ability to link back to a carbon-life form helps support the end to end traceability of agent events and transactions – even if the resources being accessed are across business or operational boundaries.
The rise and complexity of agentic-AI will continue throughout 2026. It is becoming a critical capability for organisations relying on such systems to understand the key authentication challenges this can bring as an immediate priority. More strategic approaches to just in time access and dynamic permissioning can only be built if a scalable and ephemeral identity provider model is in place.
Getting Started
The identity and security management of the entire AI ecosystem requires both a strategic operational understanding, but also an end to end view of the identities, accounts and credentials engaging with it.
| First | Next | Iterate |
|---|---|---|
|
|
|
Put Principles Into Action with Akeyless
Akeyless helps organizations operationalize these recommendations by issuing secretless, short-lived identities for AI agents and workloads and providing centralized visibility into identities and credentials across cloud and on-prem environments. Teams can discover hard-coded or long-lived secrets, replace static credentials with rotatable or Just-In-Time access, and continuously audit which agents access which resources under defined policies.
About The Author
Simon Moffatt has over 25 years experience in IAM, cyber and identity security. He is founder of The Cyber Hut – a specialist research and advisory firm based out of the UK. He is author of CIAM Design Fundamentals and IAM at 2035: A Future Guide to Identity Security. He is a Fellow of the Chartered Institute of Information Security, a regular keynote speaker and a strategic advisor to entities in the public and private sectors.




