Vaultless® Secrets Management
Centralize and secure credentials, certificates, and keys across your CI/CD pipeline, reducing both the cost and complexity of vault management.
Simplify Secrets Management
Stop secrets sprawl, reduce risk, and save time
Our cloud-native SaaS platform provides comprehensive visibility, control, and top-tier security for all secret types across multiple cloud and DevOps environments.

Use Cases
Automate DevOps Tasks
Free DevOps teams from the burden of manual secrets management
Our developer-first platform fits seamlessly into your CI/CD pipeline and dev tools.
-
Automated Credential Rotation
-
Just-in-time Secrets
-
Short-lived SSH Certificates
-
Secure Secret Sharing
Reduce Cost and Complexity
Akeyless SaaS secrets management is easy to use, manage, deploy and scale
No maintenance required—no vaults to maintain or upgrade.
Akeyless makes Secrets Management simple and secure for your teams.
Prevent #1 Cause of Breaches
Akeyless is the industry’s most secure SaaS secrets management platform
Stay in complete control of your secrets with our revolutionary approach to cryptography operations using globally distributed, constantly refreshed fragments of your encryption key.
Trusted by Customers, Partners,
and Industry Experts
Ready to Take Control of Your Machine Identities and Secrets?
Resources
-
Akeyless: The Leading HashiCorp Vault Alternative In this video blog, Sam Gabrail explains why Akeyless leads over HashiCorp Vault, with features like automated rotation and universal identity.
-
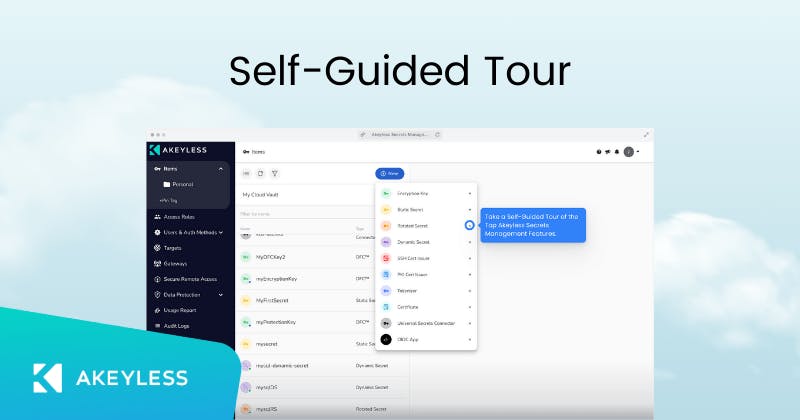
Self-Guided Product Tour Explore Akeyless secrets management on a self-guided product tour.
-
Explore Breaking the Chain: Secrets Management in the MITRE ATT&CK Framework