DevOps | InfoSec | Security
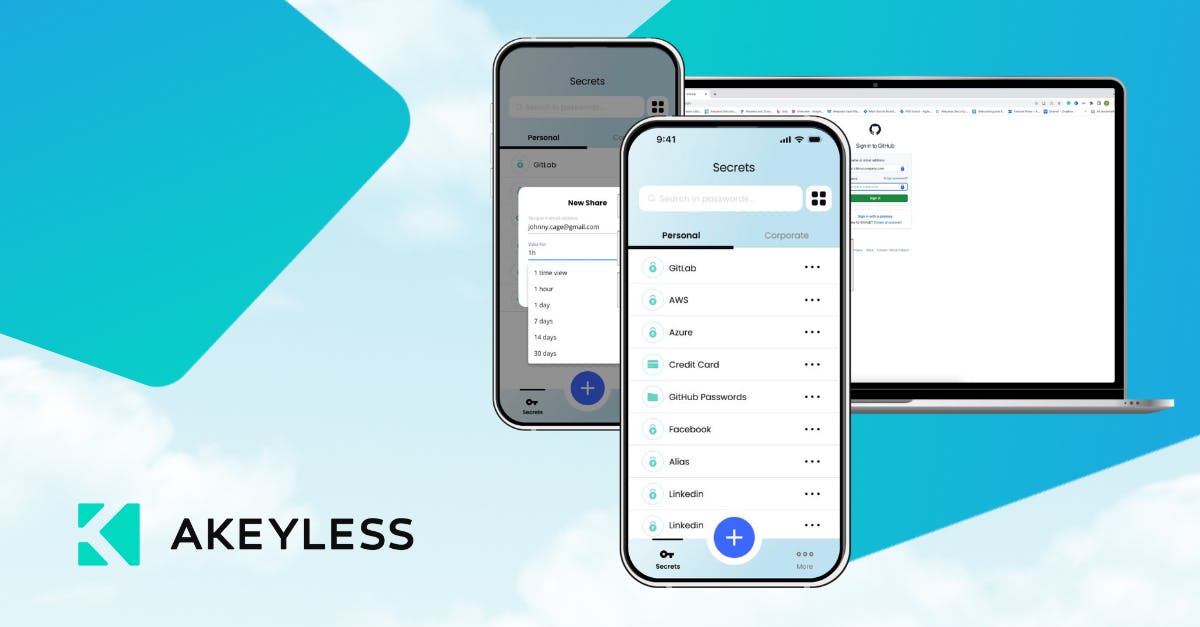
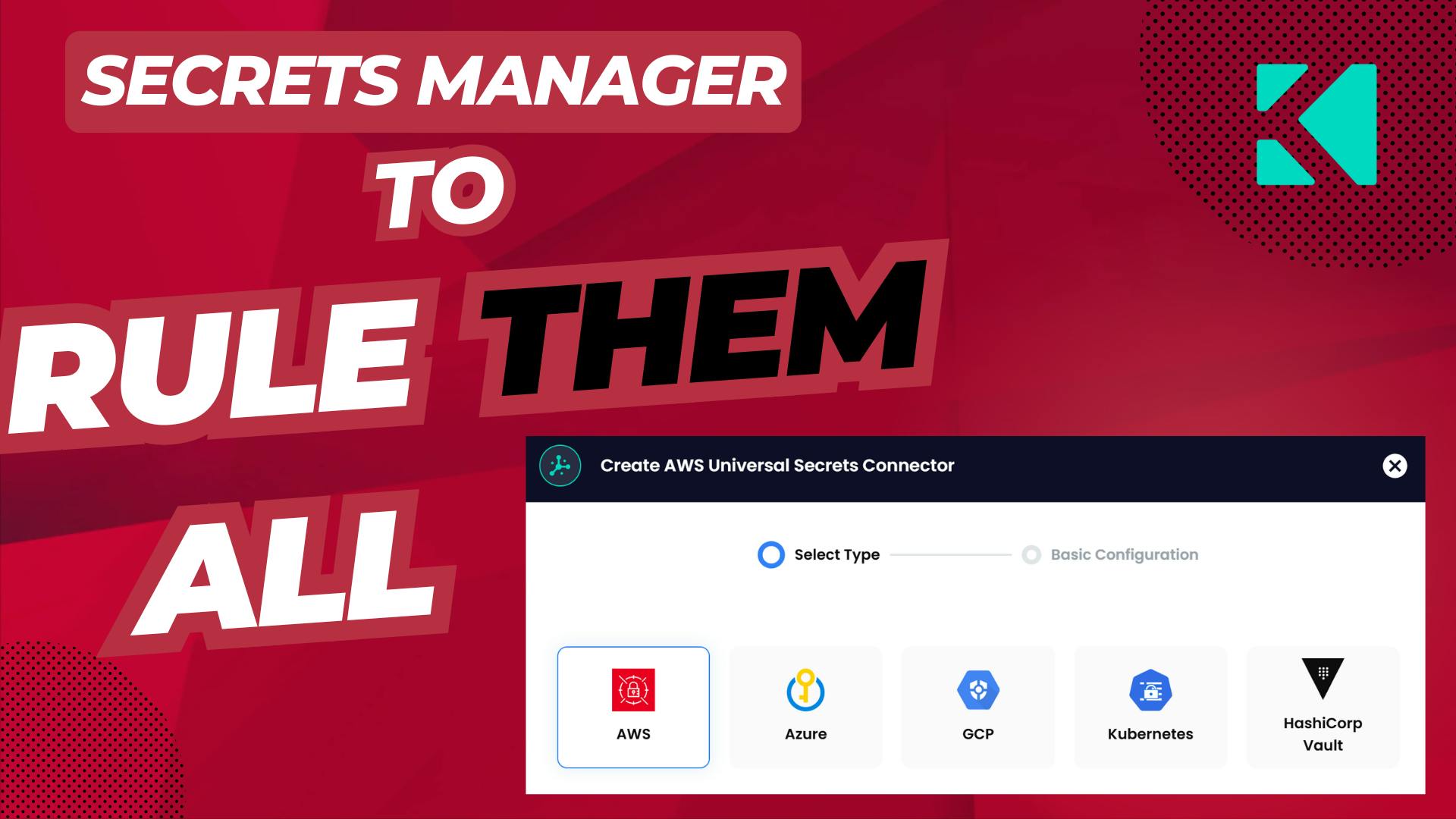
Centralized Secrets Management: Eliminate Silos with Akeyless Universal Secrets ConnectorAs organizations adopt hybrid cloud environments, secrets management has become critical to security and operational efficiency. Platform engineers often seek to centralize secrets management with a single tool, but development teams may be tied to specific options like AWS Secrets Manager or Google Secret Manager due to unique requirements. Akeyless Universal Secrets Connector (USC) unites all your secrets managers, solving the chaos with a single access point—without forcing migration. By providing a centralized platform, Akeyless USC simplifies administration, enhances security by enforcing consistent policies, and boosts productivity across the enterprise.